Best Practices
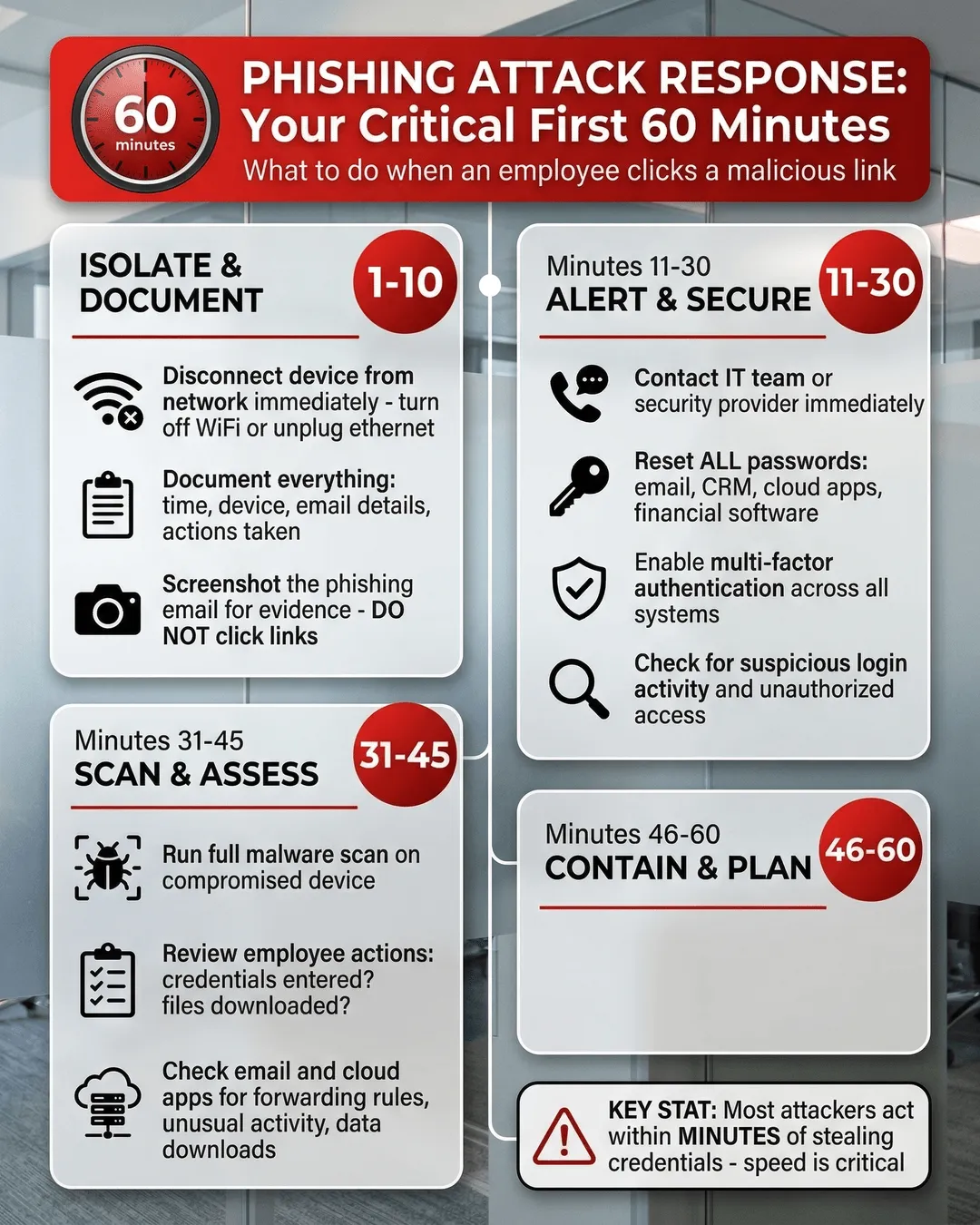
The clock starts ticking the moment someone clicks a malicious link. What you do in the next hour determines whether it is a scare or a full-blown breach.
When an employee clicks a phishing link, your response in the first 60 minutes determines whether you face a minor scare or a major breach. This guide walks business leaders through immediate containment, credential resets, malware scanning, and recovery steps to protect your organization.