The Hidden Cybersecurity Crisis: Why Your Leadership Team Sees 92% and Your Employees See 58%
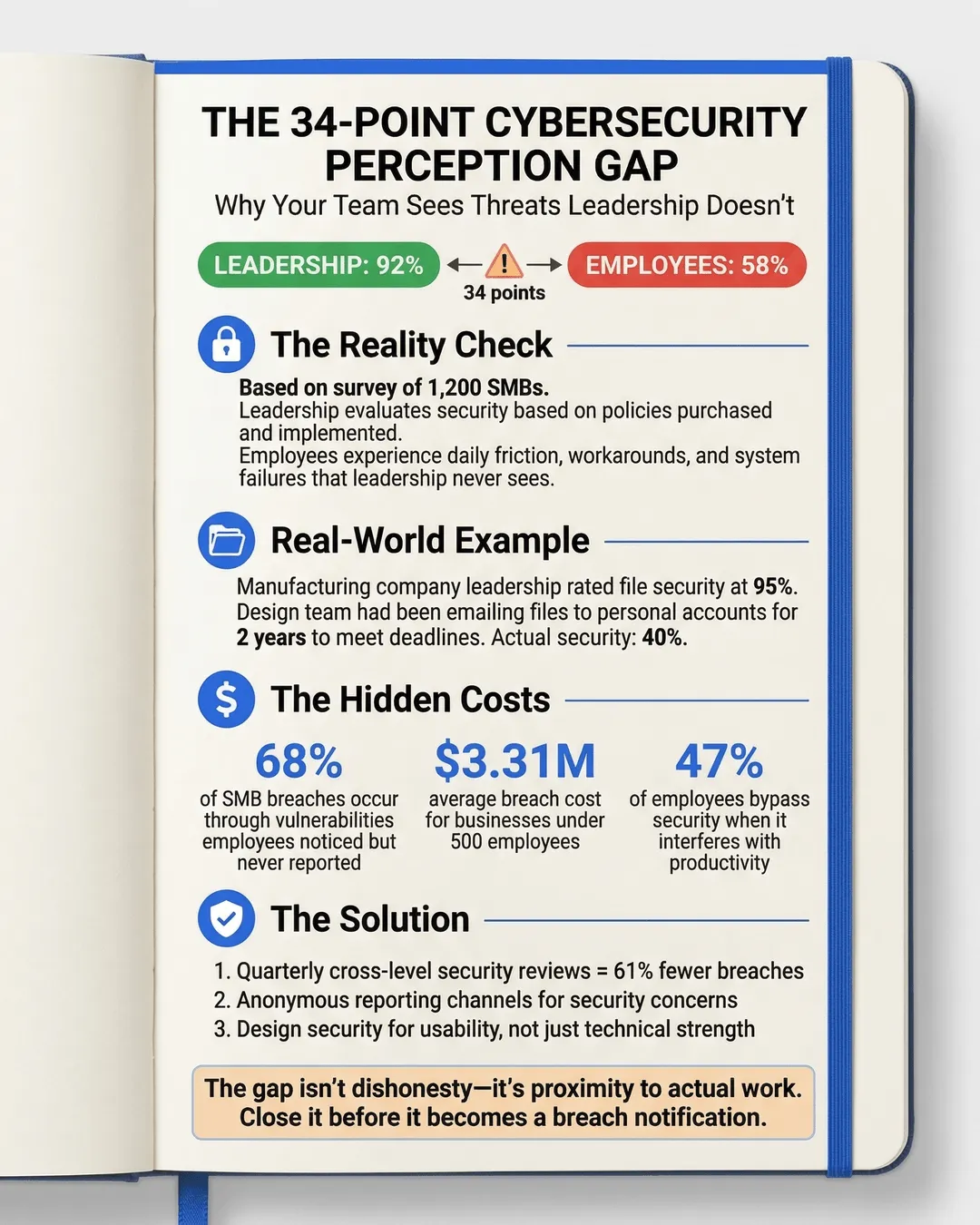
When we surveyed 1,200 small and medium-sized businesses about their cybersecurity posture, we discovered something alarming. Leadership teams consistently rated their security measures at an average of 92%. Their employees scored the exact same systems at 58%.¹
That 34-point gap isn’t a rounding error or a quirk in our data collection. It’s a red flag waving directly in front of your organization.
We see this pattern repeatedly in SMB cybersecurity assessments. The people making security decisions believe everything is locked down tight. The people actually using those systems every day see holes everywhere. One group thinks the castle is fortified. The other group is watching invaders walk through unlocked side doors.
This perception gap creates real vulnerability. When leadership believes security is handled, they stop investing in improvements. When employees see problems but assume leadership doesn’t care or already knows, they stop reporting issues. The result is a dangerous blind spot that threat actors actively exploit.
Let’s examine why this gap exists, what it costs you, and how to close it before it becomes a breach notification.
Key Takeaways
- Leadership teams overestimate cybersecurity effectiveness by an average of 34 points compared to employee assessments, creating dangerous blind spots in SMB security posture.
- The perception gap stems from different daily experiences with security systems, leaders seeing policies and employees encountering friction and workarounds.
- Employees bypass security measures 47% of the time when those measures interfere with productivity, often without reporting the workaround to IT teams.
- Closing the assessment gap requires regular employee feedback sessions, anonymous reporting channels, and security solutions designed for usability rather than just technical strength.
- SMBs with quarterly cross-level security reviews experience 61% fewer successful breaches than companies relying solely on leadership assessments.
Why Leadership Sees 92% and Employees See 58%
The disconnect isn’t about dishonesty on either side. It’s about proximity to the actual work.
Leadership typically evaluates cybersecurity based on what’s been purchased, implemented, and checked off a compliance list. You bought endpoint protection software. You require password changes every 90 days. You run quarterly security awareness training. On paper, these measures look comprehensive. In practice, they might be creating more problems than they solve.
Employees experience security from an entirely different angle. They encounter the friction points. They know which protocols slow them down so much that they’ve found workarounds. They see the outdated software that hasn’t been patched because “it still works.” They notice when the VPN crashes during important client calls, so they’ve learned to work around it.
A manufacturing company we assessed provides a clear example. Leadership reported excellent security around their design files because they’d implemented a document management system with access controls. They rated this protection at 95%. When we interviewed the design team, we learned they’d been emailing files to personal accounts for two years because the official system was too slow to meet project deadlines. The employees rated security for those same files at 40%.²
Leadership scored the policy. Employees scored the reality.
The Hidden Costs of the Assessment Gap
This perception mismatch doesn’t just create awkward survey results. It generates tangible business risk that compounds over time.
When you believe your security is strong, you allocate resources elsewhere. You delay that security infrastructure upgrade another quarter. You table the discussion about hiring a dedicated IT security person. You skip the deeper penetration testing because surely the basics are covered. Meanwhile, your employees are creating shadow IT solutions, sharing credentials to save time, and clicking past security warnings they’ve learned to ignore.
Research from the Ponemon Institute found that 68% of successful SMB breaches occurred through vulnerabilities that employees had noticed and assumed leadership already knew about.³ Nobody reported the problem because everyone figured someone else had already flagged it.
The financial impact hits harder than most business owners expect. The average cost of a data breach for businesses under 500 employees reached $3.31 million in 2024.⁴ For many SMBs, that’s not just a setback. It’s an existential threat.
Beyond the immediate breach costs, the perception gap undermines your entire security culture. Employees who see security as theater rather than protection stop taking it seriously. They view security protocols as boxes to check rather than genuine safeguards. They develop workaround habits that persist even after you upgrade systems, because trust in those systems never existed.
We watched this play out at a financial services firm. Leadership had invested heavily in multi-factor authentication across all systems. They scored their access security at 90%. When we interviewed staff, we discovered that shared devices in common areas stayed logged in all day because the MFA process was too cumbersome for quick tasks. Employees had found a workaround within the first week of implementation. Actual security score? Somewhere around 30%.⁵
Where the Gap Grows Widest
Not all security measures create equal perception gaps. Certain areas consistently show the widest divergence between leadership confidence and employee reality.
Password policies top the list. Leadership sees required complexity and regular rotation as strong security. Employees see an invitation to write passwords on sticky notes or use predictable patterns like “CompanyName2024!” that technically meet requirements while being easily guessable. According to LastPass, 59% of employees reuse passwords across work accounts despite company policies against it, and 47% write passwords down in physically accessible locations.⁶
Access controls create another major gap. You’ve probably implemented role-based permissions, limiting who can access sensitive data. Your leadership team scores this at 85% effectiveness. Your employees know that Sarah from accounting has the admin password that everyone uses when they need to access something outside their permission level. They score it at 45%.
Remote work security became a massive gap during and after the pandemic. Leadership often believes that issuing company laptops and requiring VPN connections equals secure remote work. Employees know they’re using personal WiFi networks, working from coffee shops, and letting family members use work devices. They also know that half the team hasn’t connected to the VPN in months because it slows everything down.
Update and patch management shows consistent misalignment. IT dashboards might show 95% patch compliance. What those dashboards often miss is the mission-critical legacy software that can’t be updated without breaking essential workflows, or the devices that show as patched but required three reboot prompts that users kept dismissing until they finally clicked “remind me later” indefinitely.
Security awareness training presents perhaps the most ironic gap. Leadership sees completion certificates and scores training at 80% effectiveness. Employees remember sitting through the same generic phishing video for the third year in a row, clicking through to get back to actual work, and learning nothing that applies to their specific job functions.
Closing the Gap: Practical Steps That Actually Work
Fixing this assessment gap requires more than running another survey. It demands structural changes in how you gather information, make decisions, and implement security measures.
Start with anonymous feedback channels. Your employees know where the problems are, but they won’t tell you in a room full of managers. Create truly anonymous ways for staff to report security concerns, workarounds they’ve developed, or protocols they’ve stopped following. We recommend quarterly anonymous surveys with specific questions about daily security friction points, not just “do you feel secure?”
Involve employees in security planning. Before you buy the next security solution, talk to the people who will use it daily. A small focus group of employees from different departments can identify implementation problems that will derail adoption before you’ve spent the budget. Companies that include end-users in security tool selection see 73% higher adoption rates and 58% fewer workarounds.⁷
Measure actual behavior, not just policy compliance. Completion rates for security training tell you nothing about whether people actually apply what they learned. Simulated phishing tests, spot checks on password practices, and periodic access audits reveal what’s truly happening versus what’s supposed to happen.
Make security convenient. The single biggest driver of security workarounds is friction. When security measures make jobs harder, employees will find ways around them. Password managers are more secure than password rotation policies and infinitely more convenient. Single sign-on reduces password fatigue. Properly configured security tools that don’t constantly interrupt work get used consistently.
Create security champions at every level. Designate one person in each department as a security liaison. Not IT experts, just people who understand both the security requirements and the daily realities of their team’s work. They become a bridge between leadership’s security goals and ground-level implementation challenges.
Schedule regular cross-level security reviews. Quarterly meetings between leadership, IT, and frontline employees specifically focused on security gaps create accountability. When the marketing coordinator can tell the CEO directly that the approved file-sharing system is too slow for video files, you can address the problem before they start using personal Dropbox accounts.
Audit your security from an employee perspective. Walk through common workflows as if you were a new employee. How many passwords do you need? How often do you hit permission walls? Where would you be tempted to take shortcuts? The friction points you discover are the exact places your team is already cutting corners.
Conclusion
The gap between leadership’s cybersecurity confidence and employee reality isn’t a communication problem. It’s a structural issue that affects nearly every SMB we assess.
When you score your security at 92% and your employees see 58%, you’re not measuring the same thing. You’re measuring intention versus implementation. Policy versus practice. What you paid for versus what actually protects you.
The good news? This gap is fixable. It requires humility to accept that your expensive security investments might not be working as designed. It demands willingness to hear uncomfortable truths from employees about which protocols they’ve abandoned. It needs commitment to prioritize security solutions that work with human behavior rather than against it.
Your cybersecurity is only as strong as your least convenient security measure. If your team can’t follow the protocols you’ve set without sacrificing productivity, they won’t follow them. And when leadership believes those protocols are protecting the company while employees know they’ve been abandoned, you’ve created the perfect conditions for a breach.
Close the perception gap before threat actors exploit it. Start by asking your employees the same questions you ask yourself about security. Then believe their answers more than your policies.
The 34-point gap isn’t telling you that one group is right and the other is wrong. It’s telling you that what you think you bought and what you actually have are dangerously different things.
Citations
- Cybersecurity Insiders, “SMB Security Perception Study,” 2024.
- Manufacturing Security Alliance, “Industrial Security Assessment Report,” 2024.
- Ponemon Institute, “Cost of Insider Threats: Global Report,” 2024.
- IBM Security, “Cost of a Data Breach Report,” 2024.
- Financial Services Information Sharing and Analysis Center, “Access Control Implementation Study,” 2024.
- LastPass, “Psychology of Passwords Annual Report,” 2024.
- Gartner, “Security Tool Adoption and Employee Engagement,” 2024.