Business email compromise doesn't require malware, hacking, or technical sophistication. Just a convincing email and an employee who doesn't verify. It's devastatingly effective.
Key Takeaways
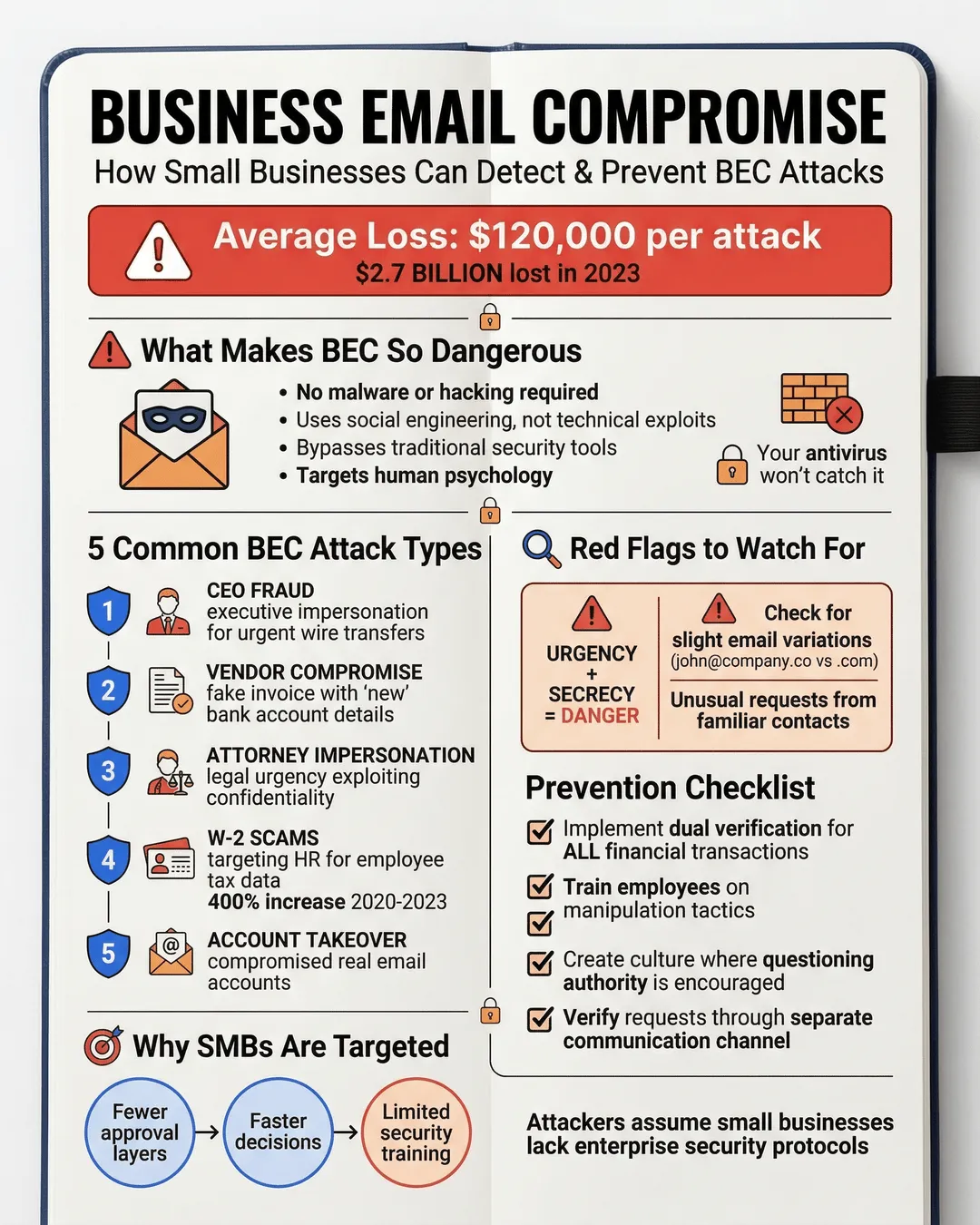
- Business email compromise (BEC) attacks rely on social engineering, not technical exploits, making them difficult to detect with traditional security tools.
- The average BEC attack costs small and medium-sized businesses $120,000, with many victims never recovering the full amount.
- Implementing dual verification processes for financial transactions and training employees to recognize urgency-based manipulation tactics can prevent most BEC attempts.
- Small businesses are increasingly targeted because attackers assume they lack the security protocols and training programs of larger enterprises.
- Creating a culture where employees feel comfortable questioning authority and verifying requests can be your strongest defense against email fraud.
Why BEC Attacks Work So Well Against Small Businesses
I’ve talked to dozens of business owners who thought they were too small to be targeted by sophisticated fraud. They invested in antivirus software, firewalls, and spam filters, then felt reasonably secure. Then one day, their bookkeeper received an email from “the CEO” requesting an urgent wire transfer to close a time-sensitive deal.
The email looked legitimate. The tone matched. The timing made sense. The money was sent.
Business email compromise attacks succeed because they exploit human psychology rather than technical vulnerabilities. According to the FBI’s Internet Crime Complaint Center, BEC attacks resulted in losses exceeding $2.7 billion in 2023, with small and medium-sized businesses representing a growing percentage of victims¹.
Here’s what makes these attacks particularly dangerous for SMBs. Large enterprises typically have multi-layered approval processes, segregated financial duties, and regular security awareness training. Small businesses often have fewer people wearing multiple hats, faster decision-making cultures, and limited time for security protocols. Attackers know this. They specifically target businesses where one or two people have authority to move money and where questioning leadership might feel uncomfortable.
The attack doesn’t announce itself with flashing warning signs. No suspicious attachments. No obvious phishing links. Just a convincing request from someone who appears to have authority. Your spam filter won’t catch it because technically, it’s not spam. Your antivirus won’t flag it because there’s no malicious code. The email passes through your defenses completely undetected.
The Most Common BEC Attack Patterns Targeting SMBs
BEC attacks follow predictable patterns once you know what to look for. Understanding these patterns helps you build defenses before an attack happens.
CEO fraud remains the most common variant. An attacker impersonates your company’s executive, usually targeting someone in finance or HR. The email creates urgency around a confidential business transaction, acquisition negotiation, or legal matter. The target is instructed to wire funds or share sensitive information quickly and quietly. The request often comes when the CEO is traveling, in meetings, or otherwise unavailable to verify.
Vendor email compromise takes a different approach. Attackers research your supplier relationships, then impersonate a legitimate vendor requesting payment to a “new” bank account. They time these emails to coincide with actual invoice cycles. Your accounts payable team receives what appears to be a routine payment update from a trusted partner. The fraudulent banking details look professional and official.
Attorney impersonation leverages the authority and confidentiality associated with legal matters. Attackers pose as lawyers handling time-sensitive transactions, settlements, or regulatory issues. The emails create artificial urgency while discouraging verification through references to attorney-client privilege or confidential negotiations.
W-2 scams specifically target HR departments during tax season. An attacker impersonating executive leadership requests employee W-2 forms for a legitimate-sounding business purpose. The target complies, unknowingly handing over sensitive personal information for the entire workforce. According to the IRS, these attacks increased by 400% between 2020 and 2023, with small businesses particularly vulnerable².
Account compromise represents the most sophisticated variant. Instead of spoofing an email address, attackers gain access to a legitimate business email account through credential theft. They monitor email patterns, learn communication styles, and wait for opportune moments to insert fraudulent requests. Because the emails originate from genuine accounts, they bypass most security measures and raise fewer suspicions.
How to Detect BEC Attempts Before Money Moves
Detection requires training your team to recognize behavioral red flags rather than technical indicators. I recommend focusing on these specific warning signs.
Urgency combined with secrecy is the biggest tell. Legitimate business transactions rarely require both speed and confidentiality simultaneously. When an email creates artificial pressure to act quickly while discouraging normal verification processes, pause. Real executives understand that financial controls exist for good reasons. They don’t bypass them for convenience.
Slight variations in email addresses often reveal impersonation attempts. Instead of john@yourcompany.com, the attacker uses john@yourcompany.co or john@your-company.com. These variations are easy to miss during a busy workday. Train your team to hover over sender names to reveal the actual email address before responding to any financial request.
Unusual requests from familiar contacts deserve extra scrutiny. If your CEO has never requested a wire transfer via email before, the first time shouldn’t happen without verification. If a vendor suddenly changes payment information after years of consistency, that’s worth a phone call. Changes in communication patterns, tone, or process should trigger verification steps.
Requests to bypass normal procedures signal potential fraud. Legitimate business needs occasionally require expedited processes, but they don’t typically require circumventing all controls. When an email explicitly instructs you to “handle this quietly” or “don’t discuss with the team,” that’s a manipulation tactic, not a business necessity.
Generic greetings and vague language can indicate mass-targeted attempts. While sophisticated attackers customize their messages, many still use templates. Emails that lack specific details about ongoing projects, use formal language in otherwise casual organizations, or include subtle grammatical inconsistencies warrant additional verification.
I recommend implementing a simple verification protocol: Any financial request or sensitive data request received via email must be confirmed through a separate communication channel before action. Call the person directly using a known phone number, not one provided in the email. Send a text message. Walk to their office. This single step prevents the vast majority of BEC attacks.
Practical Prevention Strategies for Resource-Constrained SMBs
You don’t need enterprise-level security budgets to protect against BEC attacks. You need clear policies, consistent training, and a culture that prioritizes verification over speed.
Establish dual verification for financial transactions. Any payment request above a threshold amount (I suggest $5,000 for most SMBs, but adjust based on your business) requires confirmation from two people through separate communication channels. This creates friction, but that friction has value. It forces a pause before money moves.
Create explicit protocols for changing payment information. Vendor banking details should only be updated after verification through a documented process. A single email is never sufficient. Require a phone call to a known number plus written confirmation through your vendor portal or a separate email thread. Yes, this takes extra time. That time is significantly cheaper than recovering from fraud.
Train employees regularly on social engineering tactics. Annual security training isn’t enough. BEC attack methods evolve constantly. I recommend quarterly 15-minute refreshers focusing on real-world examples. Share recent attack attempts (anonymized if they targeted your company). Make the training relevant to each person’s role and responsibilities.
Implement email authentication protocols. DMARC, SPF, and DKIM aren’t perfect, but they make email spoofing significantly harder. According to Valimail’s 2024 Email Fraud Landscape report, organizations with properly configured DMARC policies experienced 72% fewer successful email impersonation attempts³. These technical measures won’t prevent account compromise, but they block the easier spoofing attacks.
Build a culture where questioning is encouraged. This might be the most important defense and the hardest to implement. Employees need to feel comfortable verifying requests from executives without fear of appearing insubordinate or incompetent. When someone follows protocol and verifies a legitimate request, acknowledge that behavior positively. When someone catches a fraudulent attempt, celebrate it. The moment verification becomes awkward or discouraged, you become vulnerable.
Limit publicly available information about your organizational structure. Attackers research targets through company websites, LinkedIn profiles, and social media. You don’t need to be secretive, but consider what information helps criminals construct convincing impersonations. Do you need to list your CFO’s email address publicly? Should your CEO’s travel schedule be visible on social media?
Use separate communication channels for sensitive requests. Some organizations implement policies where financial requests must be initiated through accounting software or project management tools rather than email. Others require that any request above certain thresholds be submitted through a web portal with multi-factor authentication. These approaches remove email from the process entirely for high-risk transactions.
What To Do If You Suspect or Confirm a BEC Attack
Speed matters when you discover a BEC attempt or realize you’ve been compromised. Here’s what to do immediately.
If you identify a suspicious email before taking action, preserve it completely. Don’t delete it or forward it multiple times, which can strip metadata. Take screenshots showing the full header information. Report it to your IT team or provider. Share details with colleagues who might receive similar attempts.
If money has already been transferred, contact your bank immediately. The FBI reports that rapid reporting can sometimes enable recovery through bank cooperation, particularly for domestic transfers⁴. You have a brief window, usually measured in hours, before funds are moved to secondary accounts or converted to untraceable forms.
File reports with the FBI’s IC3 (Internet Crime Complaint Center) and local law enforcement. While recovery rates remain low, reporting creates records that help authorities track patterns and potentially identify perpetrators. Some cyber insurance policies require prompt reporting to maintain coverage.
If an email account was compromised rather than spoofed, assume the attacker accessed all emails in that account. Change passwords immediately across all systems. Enable multi-factor authentication everywhere possible. Review sent items for fraudulent messages. Check email rules or forwards the attacker might have created to maintain access or monitor communications.
Inform potentially affected partners, vendors, and customers. If the compromised account was used to send fraudulent requests to external contacts, they need to know those communications weren’t legitimate. Yes, this is uncomfortable. It’s also necessary and demonstrates integrity.
Conduct a post-incident review regardless of outcome. What controls failed? What warning signs were missed? What processes need adjustment? The goal isn’t to assign blame but to strengthen defenses. Every attempted attack, successful or not, provides learning opportunities.
Conclusion
Business email compromise prevention doesn’t require sophisticated technical solutions or massive security budgets. It requires awareness, protocols, and culture. The attacks work because they exploit trust and authority within organizations. Your strongest defense is building systems where trust is paired with verification.
Small businesses face unique challenges. You move fast, wear multiple hats, and value relationships over bureaucracy. These are strengths in most contexts. In BEC prevention, they become vulnerabilities unless you deliberately create friction around high-risk transactions.
Start with one change this week. Implement dual verification for payments above a threshold. Train your team on urgency-based manipulation. Create a culture where questioning requests is praised rather than punished. These steps won’t eliminate all risk, but they dramatically reduce your vulnerability to attacks that devastate hundreds of small businesses every day.
The next BEC attempt targeting your business might arrive tomorrow. When it does, will your team recognize it?
Citations
- Federal Bureau of Investigation, “Internet Crime Report 2023,” 2024.
- Internal Revenue Service, “W-2 Phishing Scams Targeting HR Departments,” 2023.
- Valimail, “Email Fraud Landscape Report,” 2024.
- Federal Bureau of Investigation, “Business Email Compromise: The 12 Billion Dollar Scam,” 2024.