Hackers do not always break in through code. Sometimes they just ask nicely and your employees hand over the keys.
You can install firewalls, encrypt everything twice, and require 47-character passwords with symbols that don’t exist on most keyboards. But none of that matters if someone calls your receptionist pretending to be from IT and walks away with your admin credentials.
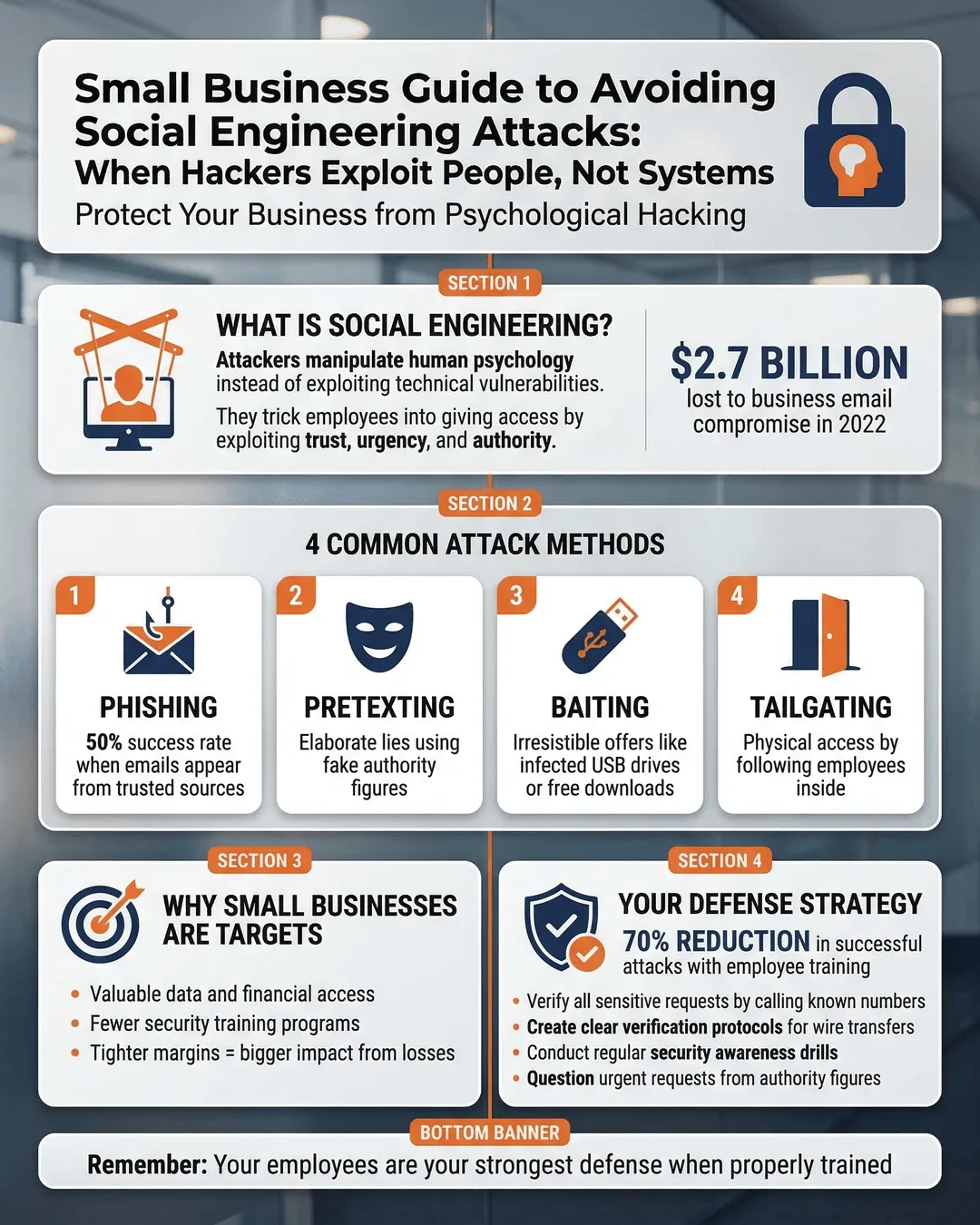
Social engineering attacks have become the preferred entry point for cybercriminals targeting small businesses. Why bother cracking complex code when you can just manipulate people into giving you what you need? A 2024 IBM Security report found that 16% of data breaches involved social engineering tactics¹, and small businesses face disproportionate risk because they often lack the security awareness programs that protect larger enterprises.
The good news is that with the right knowledge and a few practical safeguards, you can protect your business from these manipulation tactics. This guide breaks down how social engineering attacks work and what you can do to keep your team from accidentally becoming accomplices.
Key Takeaways
- Social engineering attacks exploit human psychology rather than technical vulnerabilities, making employee awareness your first line of defense.
- Common attack methods include phishing emails, pretexting phone calls, baiting with infected devices, and tailgating into secure areas.
- Warning signs include urgent requests for sensitive information, requests to bypass normal procedures, and communications that create artificial time pressure.
- Effective prevention requires both technical controls like email filtering and human-focused strategies like regular security awareness training.
- Creating a security-conscious culture where employees feel comfortable questioning suspicious requests significantly reduces your vulnerability to manipulation attacks.
What Social Engineering Actually Looks Like (And Why It Works So Well)
Social engineering is the art of manipulating people into divulging confidential information or performing actions that compromise security. Instead of exploiting software vulnerabilities, attackers exploit human nature: our tendency to trust, our desire to be helpful, and our discomfort with confrontation.
These attacks work because they bypass your technical defenses entirely. Your expensive security software cannot stop an employee from clicking a link in what appears to be an urgent message from the CEO. Your multi-factor authentication does not help if someone convinces your office manager to read the verification code out loud over the phone.
The psychology behind these attacks is surprisingly simple. Attackers create scenarios that trigger emotional responses like fear, curiosity, greed, or the desire to help. They might pose as a stressed vendor who needs payment information updated immediately, a new employee who forgot their login credentials, or an IT administrator conducting urgent security checks.
According to Proofpoint’s 2024 State of the Phish report, 68% of employees admit to engaging in risky behaviors like clicking unknown links or sharing credentials when pressured².
The financial impact hits small businesses particularly hard. The 2024 Verizon Data Breach Investigations Report revealed that small businesses experienced median losses of $46,000 per social engineering incident³. For many small companies, that represents a significant portion of annual revenue.
The Most Common Social Engineering Tactics Targeting Small Businesses
Understanding the specific methods attackers use helps you recognize them when they appear. Here are the techniques you are most likely to encounter.
Phishing and Spear Phishing
Phishing remains the most prevalent social engineering method. These attacks use fraudulent emails that appear to come from legitimate sources like banks, vendors, or colleagues. The emails typically contain malicious links or attachments designed to steal credentials or install malware.
Spear phishing takes this approach further by targeting specific individuals with personalized messages. An attacker might research your company structure on LinkedIn, then send your CFO an email that appears to come from the CEO requesting an urgent wire transfer. The personalization makes these attacks significantly more convincing than generic phishing attempts.
Pretexting Attacks
Pretexting involves creating a fabricated scenario to extract information. The attacker develops a believable story and assumes a role that gives them a plausible reason to request sensitive data.
Common pretexting scenarios include someone calling and claiming to be from your IT support provider who needs to verify system credentials, a supposed auditor requesting employee records, or a “vendor” updating billing information. These attacks succeed because the pretext provides a seemingly legitimate reason for the request.
Baiting Schemes
Baiting attacks leverage curiosity or greed to trick victims into compromising security. The classic example is leaving infected USB drives in a parking lot or reception area with labels like “Executive Salary Information” or “Confidential Client Data.” When curious employees plug these devices into their computers, malware installs automatically.
Digital baiting also appears in emails offering free gift cards, exclusive content, or prizes that require clicking a link or downloading a file. The Cybersecurity and Infrastructure Security Agency reported a 35% increase in baiting attacks targeting small businesses in 2024⁴.
Tailgating and Physical Social Engineering
Not all social engineering happens online. Tailgating occurs when an unauthorized person follows an employee into a restricted area. The attacker might carry boxes and ask someone to hold the door, wear a fake delivery uniform, or simply walk in behind someone with confidence as if they belong there.
Once inside, they can access computers left unlocked, photograph sensitive documents, or install physical devices that compromise your network. Small businesses with informal office environments face particular vulnerability to these physical manipulation tactics.
Business Email Compromise
Business email compromise combines multiple social engineering techniques to target financial transactions. Attackers research your company to understand vendor relationships, payment processes, and organizational hierarchy. They then use spoofed or compromised email accounts to request fraudulent payments or redirect legitimate transactions.
The FBI’s Internet Crime Complaint Center reported that business email compromise schemes resulted in over $2.9 billion in losses across all business sizes in 2023⁵.
How to Spot Social Engineering Before It’s Too Late
Recognizing social engineering attempts requires understanding the warning signs that appear across different attack methods.
Red Flags in Email Communications
Suspicious emails often contain subtle indicators that reveal their fraudulent nature. Look for slight misspellings in sender addresses like “ceo@yourcompany-secure.com” instead of your actual domain. Check for generic greetings like “Dear Valued Customer” rather than your actual name, especially in messages supposedly from people who know you.
Urgency represents another major warning sign. Messages that demand immediate action, threaten negative consequences for delay, or claim your account will be suspended create artificial time pressure designed to bypass your normal judgment.
Grammar and formatting issues also indicate potential attacks. While not all phishing emails contain obvious errors anymore, awkward phrasing, inconsistent formatting, or unusual word choices suggest the message did not originate from the claimed source.
Suspicious Request Patterns
Certain types of requests should always trigger additional verification. These include any communication requesting passwords or login credentials, requests to bypass normal approval processes, unusual payment instructions that differ from established procedures, or requests for sensitive employee or customer data.
Trust your instincts when something feels off. If a request seems unusual for the supposed sender, take time to verify through a separate communication channel. Do not use contact information provided in the suspicious message itself.
Verification Techniques That Actually Work
When you receive a suspicious request, contact the supposed sender through a known, trusted method. If someone claiming to be your bank emails requesting information, call the number on your bank statement, not the number in the email. If your “CEO” sends an unusual wire transfer request, walk to their office or call their direct line to confirm.
Create a company policy that makes verification standard practice for sensitive requests, regardless of how legitimate they appear. This removes the social pressure that makes employees reluctant to question authority figures.
Building Your Social Engineering Defense Strategy
Effective protection requires combining technical controls with human-focused training and clear policies.
Security Awareness Training That Actually Sticks
Generic, annual security training does not work. Your employees need regular, engaging education that reflects current attack methods and provides practical guidance they can apply immediately.
Implement short, frequent training sessions rather than long annual presentations. Use real-world examples from recent attacks targeting businesses similar to yours. Create simulated phishing campaigns to test employee responses and identify individuals who need additional support.
The SANS Institute found that organizations conducting monthly security awareness activities reduced successful phishing attacks by 64% compared to those with annual training⁶.
Make training relevant to different roles. Your finance team faces different risks than your sales staff, so tailor examples and scenarios accordingly.
Technical Controls That Complement Human Vigilance
Deploy email filtering systems that flag suspicious messages and block known phishing domains. Implement multi-factor authentication for all accounts, especially those with access to financial systems or sensitive data. This adds a verification step that social engineering alone cannot bypass.
Establish clear, verifiable processes for sensitive transactions. Require verbal confirmation through a known phone number for payment changes, wire transfers above certain amounts, or requests involving customer data.
Use endpoint protection that detects unusual behavior patterns, such as mass data downloads or connections to suspicious domains. Apply the principle of least privilege, giving employees access only to the systems and information they need for their specific roles.
Creating a Security-Conscious Culture
The most effective defense against social engineering is a culture where employees feel empowered to question suspicious requests without fear of appearing difficult or distrustful.
Celebrate employees who report potential attacks, even if they turn out to be false alarms. Publicly acknowledge good security judgment to reinforce positive behavior.
Establish clear reporting procedures so employees know exactly what to do when they encounter something suspicious. Make reporting easy and quick, not a bureaucratic hassle that discourages people from coming forward.
Remove blame from security conversations. When an employee falls for a social engineering attempt, treat it as a learning opportunity rather than a disciplinary issue. Fear of punishment drives incidents underground and prevents your team from developing genuine security awareness.
Conclusion
Social engineering attacks succeed because they exploit the most sophisticated system in your organization: human psychology. No amount of technical security can fully protect you if your employees remain vulnerable to manipulation.
Your defense strategy must recognize that people make security