Here's What No One Tells You About NIST-CSF Compliance
Cybersecurity frameworks can feel overwhelming. You hear acronyms thrown around in board meetings and vendor pitches, and you wonder which ones matter for your business. NIST-CSF stands out because it was designed with you in mind, regardless of your company’s size or industry.
The National Institute of Standards and Technology Cybersecurity Framework (NIST-CSF) provides a structured approach to managing cybersecurity risks. It’s not a checklist you complete once and forget. It’s a living system that grows with your business and adapts to new threats.
For small and medium-sized businesses, NIST-CSF offers something rare in the cybersecurity world: flexibility without sacrificing thoroughness. You don’t need a massive IT department or unlimited budget to implement it effectively.
Key Takeaways
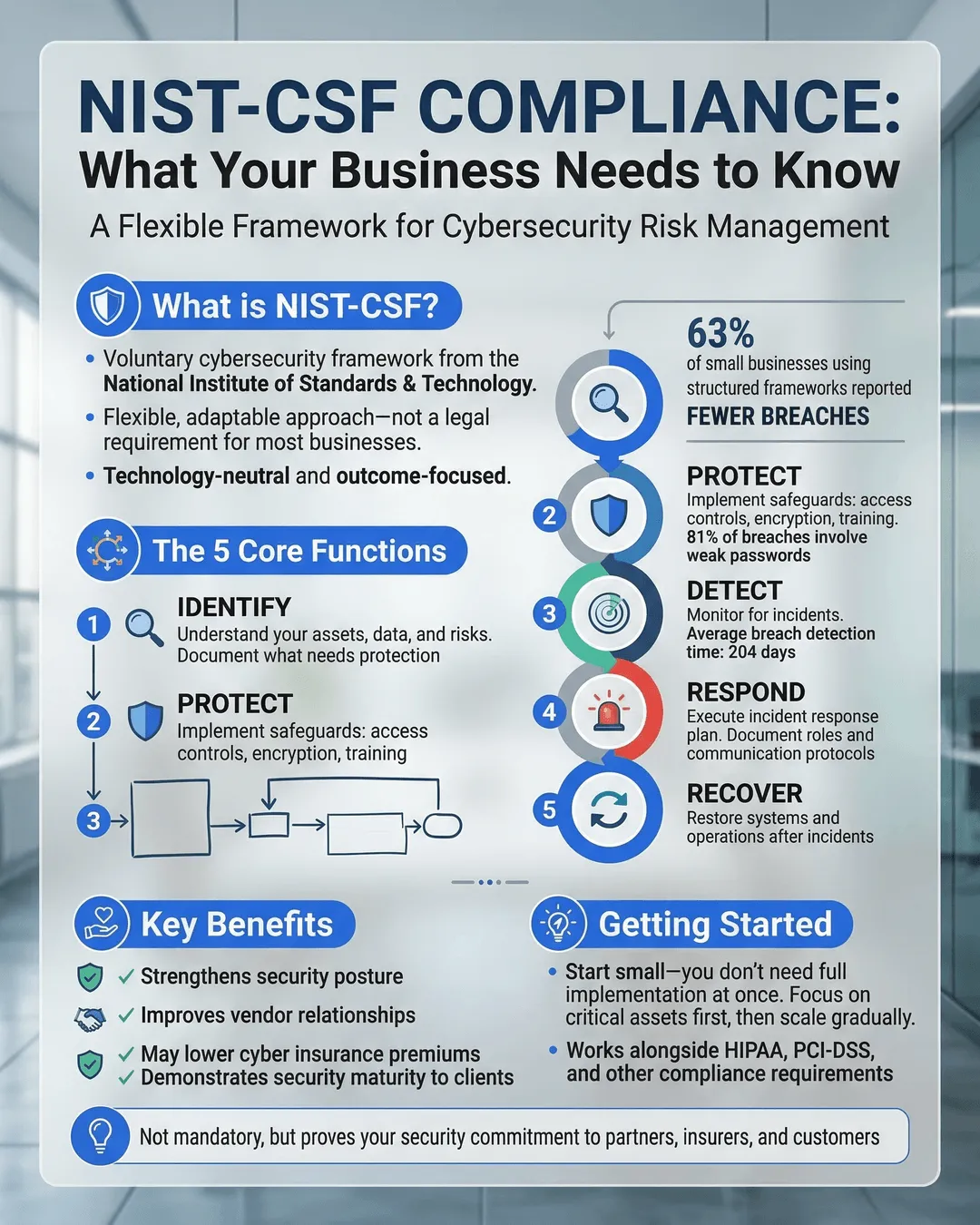
- NIST-CSF is a voluntary framework that helps organizations manage cybersecurity risk through five core functions: Identify, Protect, Detect, Respond, and Recover.
- The framework is flexible and scalable, making it accessible for SMBs without requiring extensive resources or dedicated security teams.
- Implementing NIST-CSF can reduce cyber insurance premiums by up to 15% and improve your competitive position when bidding for contracts.¹
- The framework aligns with other compliance requirements like HIPAA, PCI-DSS, and SOC 2, reducing the burden of meeting multiple standards simultaneously.
- You can start small by focusing on high-priority assets and gradually expand your implementation as your resources and maturity increase.
What NIST-CSF Actually Is (And What It Isn’t)
The NIST Cybersecurity Framework was created in 2014 after President Obama issued an executive order following a series of high-profile cyberattacks on critical infrastructure. The National Institute of Standards and Technology, a non-regulatory agency within the U.S. Department of Commerce, developed it in collaboration with private sector organizations.
NIST-CSF is not a law or regulation. It’s a voluntary set of guidelines that organizations can adopt at their own pace. This distinction matters because it gives you control over how and when you implement various components.
The framework consists of three main parts: the Core, Implementation Tiers, and Profiles. The Core contains five functions that represent the lifecycle of cybersecurity activities. Implementation Tiers help you understand your current cybersecurity maturity level. Profiles let you align your cybersecurity activities with business requirements, risk tolerance, and available resources.
Unlike prescriptive standards that tell you exactly which controls to implement, NIST-CSF lets you choose the specific security measures that make sense for your organization. If you run a healthcare practice, your priorities will differ from a manufacturing company, and the framework accommodates both approaches.
Version 2.0 of the framework was released in February 2024, adding a sixth function called “Govern” and expanding guidance for supply chain risk management and cybersecurity governance.² The update reflects the evolving threat landscape and increased recognition that cybersecurity is a business management issue, not just a technical one.
The Five Core Functions (Plus Govern)
Understanding the six core functions gives you a mental model for organizing your cybersecurity efforts. Each function addresses a different aspect of your security posture, and together they create a comprehensive approach to risk management.
Govern
The Govern function sits at the center of the framework. It establishes the context and priorities for your cybersecurity program by connecting it to your business objectives and enterprise risk management strategy.
This function addresses questions like: Who owns cybersecurity decisions in your organization? How do you allocate resources to security initiatives? What role does your leadership team play in overseeing cyber risks?
For SMBs, governance often means designating someone, whether your IT manager or an external advisor, to coordinate security efforts and report to leadership regularly. You don’t need a formal governance committee, but you do need clear accountability and regular communication about cyber risks.
Identify
The Identify function focuses on understanding your organization’s environment, assets, and risks. You cannot protect what you don’t know you have.
This includes creating an inventory of hardware and software assets, mapping data flows through your systems, understanding your supply chain dependencies, and assessing which assets are most critical to your operations.
For a small business, this might mean listing all devices that connect to your network, documenting where customer data is stored, identifying which vendors have access to your systems, and understanding which systems would cause the most disruption if they failed.
The Identify function also includes risk assessment. You evaluate the likelihood and potential impact of various threats to determine where to focus your limited resources. A retail business might prioritize payment card data protection, while a professional services firm might focus on protecting client confidential information.
Protect
The Protect function encompasses the safeguards you implement to limit or contain the impact of potential cybersecurity events. This is where most traditional security controls live.
Access control is a major component. You ensure that users can only access the data and systems they need for their jobs. This includes implementing multi-factor authentication, managing user privileges, and removing access promptly when employees leave.
Data security measures like encryption, data loss prevention, and secure backup procedures fall under this function. So do security awareness training programs that help your employees recognize phishing attempts and other social engineering tactics.
For SMBs, protective measures should be prioritized based on your risk assessment from the Identify phase. You might start with baseline protections like antivirus software, firewalls, and regular patching before moving to more advanced controls.
Detect
The Detect function involves implementing systems and processes to identify cybersecurity events in a timely manner. The faster you discover a security incident, the less damage it typically causes.
This includes monitoring network traffic for anomalies, reviewing system logs for suspicious activity, and implementing intrusion detection systems. For smaller organizations, this might mean using security tools that provide automated alerts when they spot unusual behavior.
Many SMBs struggle with detection because they lack dedicated security operations centers or 24/7 monitoring. However, managed security service providers offer affordable monitoring solutions that give smaller companies access to detection capabilities that would be prohibitively expensive to build in-house.
The Detect function also covers establishing baselines for normal network activity so you can recognize deviations. If your file server typically handles 500 transactions per hour and suddenly jumps to 50,000, that’s a signal worth investigating.
Respond
The Respond function outlines the actions you take once you’ve detected a cybersecurity incident. This includes having an incident response plan that defines roles, responsibilities, and procedures.
Your response plan should address how you contain the incident to prevent it from spreading, how you eradicate the threat from your environment, and how you communicate with stakeholders including employees, customers, and potentially regulators.
For SMBs, a response plan doesn’t need to be a 100-page document. A concise playbook that covers the most likely scenarios you might face, identifies who to contact for help (including external incident response firms or law enforcement), and provides step-by-step guidance for initial containment is often sufficient.
Testing your response plan through tabletop exercises helps identify gaps before a real incident occurs. Gather your key stakeholders and walk through a realistic scenario to see where your plan breaks down or where communication falters.
Recover
The Recover function focuses on restoring capabilities and services after a cybersecurity incident. This includes recovery planning, improvements based on lessons learned, and internal and external communications.
Your recovery plan should prioritize which systems and data to restore first based on business criticality. If your email system can wait a few hours but your point-of-sale system cannot, your plan should reflect that priority.
The Recover function also emphasizes learning from incidents. After resolving a security event, conduct a post-incident review to identify what worked, what didn’t, and what you can improve. These lessons feed back into the other functions, creating a continuous improvement cycle.
For smaller businesses, recovery often depends heavily on backups. Regularly testing your backup and restoration procedures is critical. Many organizations discover their backups are corrupted or incomplete only when they desperately need them.
Why SMBs Should Care About NIST-CSF Compliance
You might think sophisticated cybersecurity frameworks are only for large enterprises, but SMBs face significant cyber risks. In fact, 43% of cyberattacks target small businesses, yet only 14% rate their ability to mitigate cyber risks as highly effective.³
NIST-CSF gives smaller organizations a structured way to approach cybersecurity without requiring the resources of a Fortune 500 company. The framework’s flexibility means you can start with basic protections and gradually build more sophisticated capabilities as your business grows.
Cost Reduction and Efficiency
Implementing NIST-CSF can reduce your overall security spending by helping you focus resources on the controls that matter most for your specific risk profile. Rather than implementing every security control a vendor recommends, you make informed decisions based on your actual risks and priorities.
Cyber insurance is becoming increasingly important and expensive. Insurers are scrutinizing applicants’ security practices more carefully, and those with demonstrated frameworks like NIST-CSF often receive more favorable terms. Some insurers offer premium reductions of 10-15% for organizations that can demonstrate NIST-CSF alignment.¹
Competitive Advantage
Many larger companies require their vendors and partners to meet certain cybersecurity standards. By implementing NIST-CSF, you position your business to compete for contracts with larger organizations that have vendor risk management programs.
When a potential client asks about your security practices, responding with “We align our cybersecurity program with the NIST Cybersecurity Framework” sounds far more credible than “We have antivirus and firewalls.” You demonstrate that you take security seriously and manage it systematically.
Regulatory Alignment
While NIST-CSF itself is voluntary, it aligns well with various regulatory requirements. If your business operates in a regulated industry like healthcare or finance, implementing NIST-CSF can help you meet specific compliance obligations.
The framework maps to requirements in HIPAA, PCI-DSS, SOC 2, and other standards. This means work you do to implement NIST-CSF often helps you meet multiple compliance obligations simultaneously, reducing the total effort required.
Incident Response Preparedness
The average cost of a data breach for small businesses reached $3.31 million in 2024.⁴ Beyond direct costs, breaches can damage your reputation, lead to customer attrition, and create legal liabilities.
Organizations with incident response plans and teams that regularly test them save an average of $1.49 million compared to those without such preparations.⁵ NIST-CSF’s emphasis on the Respond and Recover functions helps ensure you have plans in place before you need them.
Implementing NIST-CSF in Your SMB: A Practical Roadmap
Starting with NIST-CSF can feel daunting, but you don’t need to implement everything at once. A phased approach lets you build momentum and demonstrate value while working within resource constraints.
Phase 1: Establish Your Current State
Begin by assessing your current cybersecurity posture. Where do you stand today across the six core functions? This baseline assessment helps you identify gaps and prioritize improvements.
You can conduct this assessment internally using NIST’s resources or engage a consultant who specializes in helping SMBs with framework implementation. Many cybersecurity firms offer affordable gap assessments specifically designed for smaller organizations.
Document your critical assets and processes. What systems and data are essential to your operations? Which vendors have access to your environment? Where is sensitive information stored and who can access it?
Understanding your current state also means determining your Implementation Tier. NIST defines four tiers ranging from Partial (Tier 1) to Adaptive (Tier 4). Most SMBs start at Tier 1 or 2, with informal or somewhat formal risk management processes. Knowing your starting point helps set realistic improvement goals.
Phase 2: Define Your Target Profile
Your target profile represents where you want to be. This should align with your business objectives, risk tolerance, and available resources.
If you’re a healthcare practice handling protected health information, your target profile will emphasize data protection and access controls. If you’re a manufacturer with industrial control systems, you’ll focus more on operational technology security and supply chain risk management.
Your target profile doesn’t mean implementing everything in the framework at the highest maturity level. It means identifying which functions, categories, and subcategories are most relevant to your organization and determining an appropriate maturity level for each.
For example, you might decide that multi-factor authentication for all user accounts is a priority (high maturity) while advanced threat hunting capabilities are less critical for now (lower maturity or not implemented yet).
Phase 3: Build Your Implementation Plan
With your current state and target profile defined, create a prioritized plan to close the gaps. This plan should be realistic given your budget, staffing, and timeline constraints.
Quick wins should come first. These are high-impact, relatively easy improvements that demonstrate progress and build momentum. Installing multi-factor authentication, implementing automated patch management, and establishing regular backup procedures typically fall into this category.
Next, tackle foundational controls that support multiple framework functions. An asset inventory supports both Identify and Protect functions. Centralized logging supports Detect and Respond functions. These investments provide value across your entire program.
Finally, address more complex or resource-intensive initiatives. Advanced security tools, formal security operations capabilities, and sophisticated detection systems can come later after you’ve established strong foundations.
Phase 4: Execute and Document
As you implement controls and processes, document what you’re doing and why. Documentation serves multiple purposes: it helps with consistency and training, provides evidence for audits or customer inquiries, and facilitates continuity when team members change.
Your documentation doesn’t need to be elaborate. Simple procedures that explain how to perform key tasks, maintain security controls, and respond to incidents are often sufficient. Focus on clarity and usefulness over comprehensiveness.
Many SMBs use tools like SharePoint, Google Drive, or specialized governance, risk, and compliance platforms to maintain their documentation. Choose whatever works for your organization and ensures the information remains accessible and current.
Phase 5: Monitor and Improve
NIST-CSF is not a one-time project. Regular monitoring and continuous improvement are essential to maintaining an effective cybersecurity program.
Schedule periodic assessments to measure your progress toward your target profile. Quarterly or semi-annual reviews work well for most SMBs. These reviews let you identify where you’ve made progress, where you’ve fallen behind, and whether your priorities need adjustment based on changes in your business or threat environment.
When incidents occur, conduct post-incident reviews and feed lessons learned back into your program. These real-world tests of your controls and processes provide invaluable insights you can’t get from theoretical exercises.
Common Challenges and How to Overcome Them
Implementing NIST-CSF in an SMB environment comes with predictable challenges. Recognizing these obstacles and having strategies to address them increases your likelihood of success.
Limited Resources
The most common challenge is limited budget and staff. You don’t have dedicated security personnel, and your IT team is already stretched handling day-to-day operations.
Address this by focusing on automation and managed services. Many security functions can be automated or outsourced affordably. Managed detection and response services, cloud-based security tools with built-in automation, and virtual chief information security officer services extend your capabilities without requiring full-time hires.
Prioritization becomes even more critical with limited resources. Focus on the controls that provide the most risk reduction for your specific environment. Not every organization needs the same security controls at the same maturity level.
Lack of Executive Buy-In
Security initiatives often struggle to get leadership attention and budget allocation, especially if your organization hasn’t experienced a significant incident.
Frame cybersecurity in business terms rather than technical jargon. Discuss the potential business impact of various risks, the cost of incidents versus the cost of prevention, and how security enables business objectives like winning new customers or entering new markets.
Sharing relevant statistics and case studies from similar organizations can make risks feel more concrete. When leadership understands that 60% of small companies go out of business within six months of a cyberattack, security investments become easier to justify.⁶
Complexity and Overwhelm
The NIST-CSF framework is comprehensive, which can feel overwhelming when you’re starting. Where do you even begin?
Remember that you don’t need to implement everything immediately. Start with one or two functions that address your highest priorities. Many organizations begin with Identify and Protect, establishing what they have and implementing baseline controls before moving to more advanced capabilities.
Working with a consultant or managed security provider experienced in helping SMBs can accelerate your progress. They bring expertise and can help you avoid common pitfalls that slow implementation.
Maintaining Momentum
Initial enthusiasm often wanes as implementation drags on and competing priorities emerge. Security projects get delayed or deprioritized.
Setting specific milestones with target dates helps maintain momentum. Rather than a vague goal like “improve our security,” define concrete objectives like “implement multi-factor authentication for all users by end of Q2” or “complete asset inventory and risk assessment by end of Q3.”
Regular status updates to leadership keep security visible and reinforce its importance. Brief quarterly updates that highlight progress, upcoming initiatives, and any incidents or near-misses keep cybersecurity on the leadership agenda.
Measuring Success and Continuous Improvement
How do you know if your NIST-CSF implementation is working? Defining success metrics helps you demonstrate value and identify areas needing attention.
Quantitative Metrics
Some aspects of your cybersecurity program lend themselves to numerical measurement. These metrics provide concrete evidence of progress and can be tracked over time.
Consider measuring the percentage of assets inventoried and classified, the percentage of systems with current patches and updates, the average time to detect security events, the average time to respond to and contain incidents, and the number of employees completing security awareness training.
You might also track external metrics like customer security questionnaire scores, cyber insurance premium changes, and audit or assessment findings.
Qualitative Indicators
Other aspects of success are harder to quantify but still important. Has security awareness improved among employees? Are security considerations routinely included in business decisions? Do you have greater confidence in your ability to detect and respond to incidents?
Qualitative indicators often emerge through observation and conversation. Leadership discussions increasingly include security considerations. Employees report suspicious emails rather than ignoring them. Project teams proactively engage IT security before deploying new systems.
Maturity Progression
Tracking your Implementation Tier over time provides a high-level view of your program’s maturity. Moving from Tier 1 to Tier 2, or from Tier 2 to Tier 3, represents significant progress in how formally and effectively you manage cybersecurity risks.
This progression typically takes years, not months. Most SMBs realistically aim to reach Tier 2 or Tier 3, where risk management processes are repeatable and somewhat formalized. Tier 4, which represents adaptive and highly mature programs, is often beyond what smaller organizations need or can sustain.
Continuous Improvement Cycle
NIST-CSF is built on the principle of continuous improvement. Your threat environment changes, your business evolves, and new technologies create new risks and opportunities.
Schedule regular reviews of your cybersecurity program. Annual comprehensive reviews supplemented by quarterly check-ins work well for many organizations. These reviews should assess what’s working, what needs adjustment, and whether your priorities remain aligned with your business objectives and risk environment.
Benchmarking against peers can provide useful context. Industry groups, security vendors, and consulting firms often share benchmarking data that lets you compare your program maturity and investment levels to similar organizations.
Conclusion
NIST-CSF compliance gives your SMB a structured, flexible approach to managing cybersecurity risks. You don’t need unlimited resources or a large security team to implement the framework effectively. Start with the basics, focus on your highest priorities, and build capabilities gradually as your organization grows.
The framework’s value extends beyond security improvements. It demonstrates to customers, partners, and insurers that you take cybersecurity seriously and manage it systematically. This can open doors to new business opportunities while reducing your risk of costly incidents.
Remember that NIST-CSF is a journey, not a destination. Your implementation will evolve as your business changes and as new threats emerge. The goal is not perfect security, which doesn’t exist, but rather appropriate risk management that aligns with your business objectives and resources.
By taking the first steps toward NIST-CSF implementation, you’re investing in your business’s resilience and long-term success. The work may seem challenging at times, but the alternative, reactive security that addresses threats after they’ve caused damage, is far more costly and stressful.
Citations
- Coalition, “2024 Cyber Insurance Market Report,” 2024.
- National Institute of Standards and Technology, “NIST Cybersecurity Framework 2.0,” 2024.
- Verizon, “2024 Data Breach Investigations Report,” 2024.
- IBM Security, “Cost of a Data Breach Report 2024,” 2024.
- IBM Security, “Cost of a Data Breach Report 2024,” 2024.
- National Cyber Security Alliance, “Small Business Cybersecurity Report,” 2023.