Here's What No One Tells You About SMB Cybersecurity: Your Employees Are the Weakest Link
We spent thousands on enterprise-grade firewalls. We deployed the latest VPN infrastructure. We even hired a cybersecurity consultant who used words like “zero-trust architecture” and “next-generation threat prevention.”
Then Karen from HR clicked on an email that promised her a free Starbucks gift card.
And just like that, our entire network was compromised.
If you’re running a small or mid-sized business, this scenario probably sounds familiar. Not because it happened to you (though maybe it did), but because you know exactly who your “Karen” is. Every company has one. Sometimes several.
Here’s the uncomfortable truth about SMB cybersecurity: you can’t engineer your way out of the human problem.
Key Takeaways
- The most sophisticated cybersecurity tools cannot prevent employees from making poor security decisions.
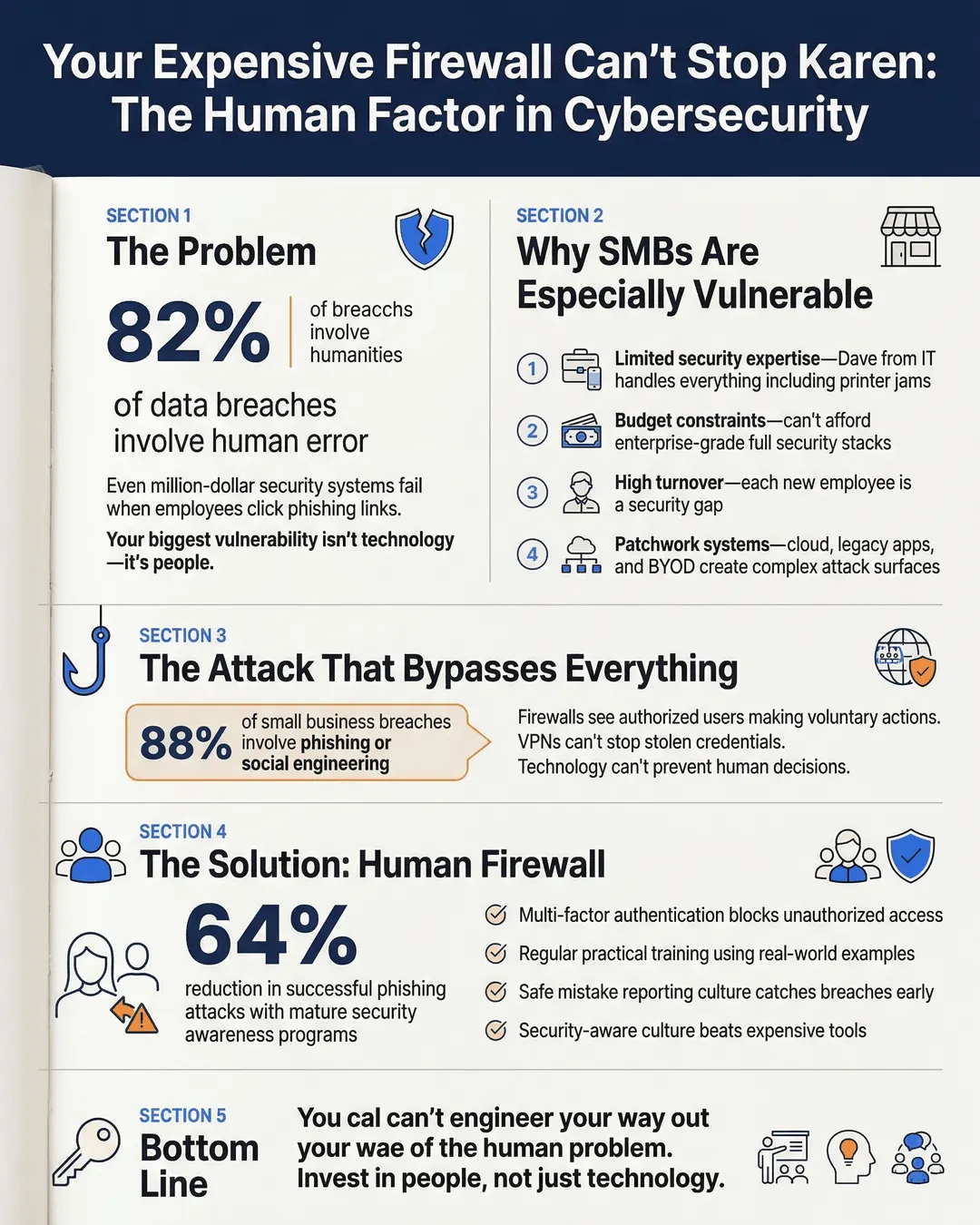
- 82% of data breaches involve human error, making employee behavior your biggest vulnerability¹.
- Small and mid-sized businesses face the same cyber threats as enterprises but typically have smaller security budgets and less specialized staff.
- A comprehensive security approach requires both technical tools and ongoing employee education.
- Simple measures like multi-factor authentication and regular security training can prevent most common attacks.
- Creating a security-aware culture is more effective than simply adding more expensive tools.
The Million-Dollar Security Stack That Still Got Hacked
Let’s talk about what most SMB leaders do when they start taking cybersecurity seriously.
First, you buy a good firewall. Maybe you spring for the fancy one with intrusion detection and all the bells and whistles. Then you set up a VPN so your remote workers can access company resources securely. You install antivirus software on every machine. You might even implement email filtering to catch phishing attempts.
You feel pretty good about yourself. You’ve checked all the boxes.
Then reality hits.
A 2024 report found that 88% of data breaches in small businesses involved phishing or social engineering attacks². Your firewall sees this traffic as completely legitimate because technically, it is. An authorized user (Karen) is voluntarily entering credentials or downloading a file. The system doesn’t know she thinks she’s claiming a prize or helping the CEO with an urgent wire transfer.
Your VPN? It keeps data encrypted in transit, which is great. But it doesn’t stop someone from accessing the VPN with stolen credentials that Karen helpfully provided to a fake IT support email.
This isn’t about bashing Karen. She’s probably good at her actual job. The problem is that we’ve built our security strategies around the assumption that technology alone will protect us. We’ve forgotten that cybersecurity is fundamentally about people making decisions.
Why Traditional SMB Cybersecurity Misses the Mark
The enterprise security model doesn’t translate well to small and mid-sized businesses. Large corporations have dedicated security operations centers, full-time security analysts, and the budget to implement defense-in-depth strategies with multiple redundant layers.
You probably have Dave from IT who also handles the printer jams.
This creates a specific set of challenges:
Limited security expertise. Most SMBs don’t employ dedicated security professionals. The person managing your firewall and VPN configuration is probably juggling ten other responsibilities. They might have the technical skills, but they don’t have the time to stay current on emerging threats or monitor security logs in real-time.
Budget constraints. Enterprise-grade security tools come with enterprise-grade price tags. Even when SMBs invest in solid technology, they often can’t afford the full stack of tools that would provide comprehensive protection. You might have a great firewall but no security information and event management system to correlate threats.
Rapidly changing workforce. Small businesses often have higher turnover and more contractors or temporary workers than large enterprises. Each new person represents a potential security gap. Training takes time and resources you might not have.
Diverse tech environments. SMBs typically run a patchwork of systems. Cloud services, legacy applications, personal devices used for work, and bring-your-own-device policies create a complex attack surface that’s harder to secure than a standardized corporate environment.
The result is a situation where you’ve invested real money in cybersecurity tools, but you still have fundamental vulnerabilities that those tools can’t address.
The Human Firewall: Your Best and Worst Defense
Here’s where we need to shift our thinking about SMB cybersecurity.
Your employees are both your greatest vulnerability and your most powerful defense. A 2025 study showed that organizations with mature security awareness programs reduced successful phishing attacks by 64%³.
That’s a better return on investment than most security tools can deliver.
But here’s the catch: security awareness training can’t be a once-a-year PowerPoint presentation that everyone clicks through while checking their phones. It needs to be ongoing, practical, and built into your company culture.
Make security training relevant and specific. Generic cybersecurity training doesn’t work because it doesn’t connect to people’s daily reality. Instead of abstract warnings about phishing, show your team actual examples of phishing emails targeting your industry. Walk them through what a fake invoice looks like. Demonstrate how to verify suspicious requests.
Create safe ways to report mistakes. Karen probably knew she shouldn’t have clicked that link the moment after she did it. But if your culture punishes mistakes, she’ll keep quiet and hope nothing bad happens. By the time your IT team discovers the breach, the damage is exponentially worse. Build an environment where people can immediately report “I think I just did something dumb” without fear of consequences.
Use positive reinforcement. When someone reports a suspicious email or catches a potential security issue, celebrate it. Make them the hero of the story. This creates a culture where security awareness is valued, not just another annoying policy to comply with.
Test regularly with simulated attacks. Run simulated phishing campaigns (using legitimate security tools designed for this purpose, not actual phishing). Track who clicks and who reports. Use failures as training opportunities, not gotcha moments.
The goal is to turn your employees into an extension of your security infrastructure, not just end users you’re defending against.
Practical Steps That Actually Work for SMBs
Let’s get specific about what works in the real world of small business cybersecurity.
Multi-factor authentication everywhere. This is non-negotiable. Even if Karen gives away her password, MFA prevents the attacker from accessing accounts without a second verification factor. Implement it for email, VPN access, financial systems, and any cloud services your team uses. Modern MFA is much easier than it used to be, with options like authenticator apps and hardware keys that don’t significantly disrupt workflow.
Update and patch religiously. Yes, updates are annoying. Yes, they sometimes break things. They also close security vulnerabilities that attackers actively exploit. Create a systematic approach to updates. For critical systems, test patches in a non-production environment first, but don’t delay implementation by months.
Segment your network. Your guest WiFi should not have access to your financial systems. Your HVAC controls (yes, attackers use these as entry points) shouldn’t be on the same network segment as your customer database. Even basic network segmentation limits how far an attacker can move if they gain initial access.
Control access based on need. Karen from HR doesn’t need admin access to your engineering systems. Your sales team doesn’t need access to payroll data. Implement least-privilege access policies. People get the access they need to do their jobs and nothing more.
Backup everything, and test your backups. Ransomware remains one of the top threats to SMBs⁴. The best defense is having clean, isolated backups you can restore from. Keep backups offline or in immutable storage that ransomware can’t encrypt. Test your restoration process regularly, because a backup you can’t restore is worthless.
Use a password manager. Stop writing passwords on sticky notes. Stop reusing the same password across multiple services. A business password manager makes it easy for your team to use strong, unique passwords for every service while keeping IT in control of access.
Monitor your financial systems closely. Many SMB breaches go undetected for months. Implement alerts for unusual financial activity. Review account access logs. Watch for changes to payment information or wire transfer requests that don’t follow normal procedures.
Building a Security Culture That Scales
The shift we need to make is from thinking about cybersecurity as a technical problem to recognizing it as an organizational challenge.
Security needs to be part of how your company operates, not a separate initiative owned by IT. When you onboard new employees, security training should be integrated into their first week. When you launch a new system or service, security considerations should be part of the planning process, not an afterthought.
This doesn’t mean you need to become a security expert or hire expensive consultants. It means:
Having clear policies that people actually understand. Your security policy shouldn’t require a law degree to interpret. Write guidelines in plain language. Make them accessible. Review them regularly and update them as your business changes.
Making security easy to do right. If your security measures are so cumbersome that people actively work around them, you’ve failed. Design security controls that protect without creating massive friction in daily work.
Leading by example. If leadership treats security policies as suggestions or demands exceptions for themselves, everyone else will follow that lead. When executives use MFA, take security training seriously, and follow the same protocols as everyone else, it sends a powerful message about organizational priorities.
Investing in security as a business priority, not just an IT expense. Frame security investments in terms of business continuity, customer trust, and competitive advantage. A security breach can destroy a small business. Prevention is dramatically cheaper than recovery.
The goal is to reach a point where security thinking is automatic. Where people instinctively question suspicious emails, verify unusual requests, and protect sensitive information because that’s just how things are done here.
Conclusion
We opened with a story about Karen clicking a phishing link despite expensive security infrastructure. The lesson isn’t that technology doesn’t matter. Firewalls, VPNs, and other SMB cybersecurity tools are essential components of a security strategy.
The lesson is that technology alone will never be enough.
Your small or mid-sized business faces real cybersecurity threats every day. Attackers specifically target SMBs because they often have valuable data but less sophisticated defenses than large enterprises. You need good technical controls like firewalls and VPNs as your foundation.
But you also need to invest in the human side of security. Train your people. Create a culture where security awareness is valued and mistakes can be safely reported. Make security practices easy enough that people will actually follow them.
The most expensive firewall in the world won’t stop Karen from clicking that link. But a well-trained Karen who knows what to look for, understands why it matters, and feels empowered to report suspicious activity? That’s the security upgrade that actually makes a difference.
Because at the end of the day, cybersecurity isn’t about building higher walls. It’s about teaching everyone in your organization to recognize when someone’s trying to climb them.
Citations
- IBM Security, “Cost of a Data Breach Report 2024,” 2024.
- Verizon, “2024 Data Breach Investigations Report,” 2024.
- KnowBe4, “2025 Phishing Security Test Benchmarking Report,” 2025.
- Cybersecurity & Infrastructure Security Agency, “SMB Ransomware Threat Assessment,” 2024.