Sensitive documents left on desks, unlocked file cabinets, and sticky notes with passwords are all physical security failures that lead to digital breaches.
Sensitive documents left on desks, unlocked file cabinets, and sticky notes with passwords are all physical security failures that lead to digital breaches.
You’ve invested thousands in firewalls, encryption, and cybersecurity training. Your IT team locks down networks, patches vulnerabilities, and monitors for threats around the clock. But here’s the uncomfortable truth: all that effort means nothing when someone walks past an empty desk and photographs sensitive client data sitting in plain view.
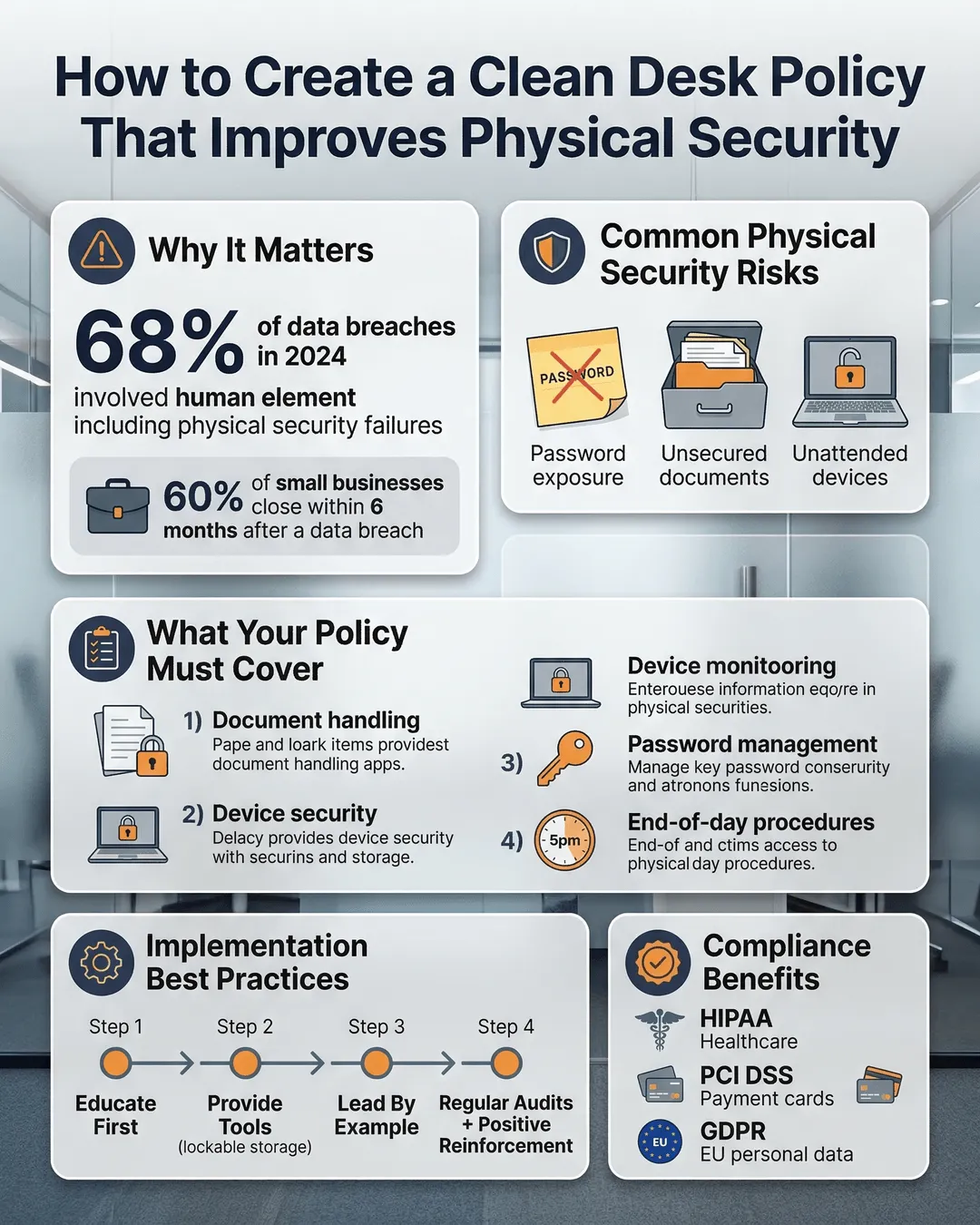
Physical security gaps are the silent killers of otherwise solid cybersecurity programs. A 2024 study found that 68% of data breaches involved a human element, and physical security lapses accounted for 12% of all confirmed breaches¹. That sticky note with a password? The contract left face-up on a conference table? These aren’t minor oversights. They’re open doors for competitors, malicious insiders, and anyone with a smartphone camera.
A clean desk policy cybersecurity approach closes these doors. It’s not about being obsessively tidy or creating a sterile work environment. It’s about establishing simple, consistent habits that protect your business from preventable security incidents.
Why Your Office Is More Vulnerable Than You Think
Walk through your office right now. What do you see?
If you’re like most business leaders, you’ll spot unlocked filing cabinets, printouts sitting in shared printers, whiteboards covered in project details, and desks cluttered with documents containing everything from financial projections to employee personal information. Each item represents a potential security breach waiting to happen.
The problem isn’t that your employees are careless. Most people simply don’t recognize physical documents and visible information as security risks. They’ve been trained to spot phishing emails and create strong passwords, but nobody taught them that leaving a personnel file on their desk overnight could lead to identity theft or competitive intelligence gathering.
Here’s what makes physical security particularly tricky: your building likely has more people walking through it than you realize. Cleaning crews, maintenance workers, delivery personnel, contractors, job candidates, and visitors all have legitimate reasons to be in your space. Most are trustworthy. But it only takes one person with bad intentions and a few seconds to snap photos of sensitive information.
Sarah Chen, Chief Information Security Officer at SecureWorks, puts it plainly: “Organizations spend 80% of their security budget on digital defenses and maybe 5% on physical security controls. But physical access often provides the easiest path to the data attackers want.”
Small and medium businesses face an additional challenge. You probably don’t have dedicated security personnel monitoring every floor. You rely on trust, locked doors, and the assumption that people will do the right thing. That’s not enough anymore.
Building Your Clean Desk Policy: The Core Components
A clean desk policy template doesn’t need to be complicated. The best policies are simple enough that everyone actually follows them.
Start with the clear desk requirement. At the end of each workday and during extended absences, desks must be clear of all sensitive documents and materials. This doesn’t mean your team needs to file every piece of paper every night, but anything containing confidential information needs to be secured.
Define what “sensitive” means in your organization. Create specific categories: client data, financial information, employee records, intellectual property, strategic plans, passwords or access credentials, and any proprietary research or product development materials. When people know exactly what to protect, they’re more likely to take action.
Establish storage requirements. Every employee who handles sensitive documents needs access to lockable storage. This could be filing cabinets, desk drawers with locks, or secure document boxes. The storage solution matters less than ensuring it actually gets locked. Include a policy that keys cannot be left in locks or hidden under desk mats (yes, people actually do this).
Address your printers and copiers. Implement a rule that documents cannot sit in output trays for more than 15 minutes. Better yet, require employees to use secure print release features that only print when the user is physically present at the device. This single change eliminates one of the most common physical security failures in offices.
Create a visitor protocol. Visitors should never be left unattended in areas where sensitive information is visible. This includes job candidates waiting in conference rooms, vendor representatives, and even colleagues from other departments who don’t have clearance for certain information.
Include your digital workspace. Computer screens showing sensitive data should be locked when you step away. This takes two seconds and prevents shoulder surfing and unauthorized access. Require screen timeout settings of five minutes or less on all devices.
Don’t forget mobile devices and portable storage. USB drives, external hard drives, laptops, and tablets must be secured in locked storage or taken home. They should never be left visible on desks overnight.
Implementation: Getting Your Team to Actually Follow the Policy
Writing the policy is the easy part. Getting people to follow it consistently requires a different approach.
Start with the why before the what. Schedule a company meeting or send a detailed communication explaining the real risks. Share specific examples of breaches that started with physical security failures. When people understand that a clean desk policy protects the company, their jobs, and client trust, compliance improves dramatically.
Make compliance easy. If you require locked storage but only provide it to managers, you’ve set everyone else up for failure. Invest in lockable pedestals or cabinets for every desk that handles sensitive materials. Yes, this costs money upfront. Compare that cost to a single data breach, which averaged $4.88 million for small to medium businesses in 2024².
Create visual reminders. Place small signs near exits: “Desk Clear? Documents Locked?” A gentle reminder at the moment someone is leaving often catches the things they forgot. Some organizations use color-coded folders or document sleeves that clearly mark sensitive materials.
Implement a buddy system for the first month. Pair employees and have them check each other’s workspaces at the end of the day. This builds the habit without feeling like surveillance. It also creates peer accountability, which often works better than top-down enforcement.
Make it part of your closing routine. Just as you probably have an end-of-day checklist for other business functions, add clean desk items to that workflow. For many organizations, tying it to existing habits (like shutting down your computer) helps the behavior stick.
Address the “but I’m coming back in an hour” problem. People resist cleaning their desk for lunch breaks or short meetings. Establish a clear rule: if you’re leaving your immediate work area for more than 15 minutes, sensitive documents get secured. This prevents the gradual erosion of the policy.
Training needs to be practical, not theoretical. Don’t just hand employees a PDF and expect compliance. Conduct hands-on sessions where people practice the behaviors. Show them exactly how to lock their filing cabinets, use secure print features, and identify sensitive documents. Adult learning works best when it’s demonstrable and immediately applicable.
Consider appointing clean desk champions in each department. These aren’t security police; they’re resources who can answer questions and model good behavior. When someone in accounting wonders whether a particular report needs to be locked up, they can quickly ask their department champion rather than making a guess.
Enforcement and Ongoing Management
Your clean desk policy small business approach needs teeth, but it also needs to be reasonable.
Conduct random spot checks. Have managers or HR walk through the office after hours once or twice a month. Document what they find without making it personal. If someone’s desk has sensitive information visible, that’s a coaching opportunity, not a termination offense (at least the first time).
Create a progressive discipline approach. First violation: verbal reminder and refresher training. Second violation: written warning and one-on-one meeting with their manager. Third violation: formal disciplinary action. This gives people room to adjust their habits while making it clear that the policy matters.
Track trends, not just individuals. If you notice that one department consistently struggles with compliance, that signals a training problem or a workflow issue. Maybe they handle more sensitive documents than other teams and need additional storage solutions. Address systemic problems systemically.
Build clean desk compliance into performance reviews. It doesn’t need to be a major component, but including it sends a message that physical security best practices office-wide are part of professional expectations.
Celebrate success. When your entire company maintains clean desks for a full month, acknowledge it. Positive reinforcement works better than constant criticism. Some organizations run contests or provide small rewards for departments with perfect compliance.
Update your policy annually. As your business changes, your security needs evolve. New types of sensitive information emerge, workflows shift, and technology changes what’s possible. Review and refresh your policy to keep it relevant.
Make exceptions clear and documented. Some roles genuinely require frequent access to sensitive documents throughout the day. For these positions, create specific protocols. Maybe they have additional secure storage at their desk, or they work in areas with restricted access. Document these exceptions so they don’t become loopholes.
Beyond Paper: Protecting Physical Security in a Hybrid World
The rise of hybrid and remote work creates new physical security challenges.
Home offices need clean desk policies too. When employees work from home, they need guidelines for protecting sensitive documents and data in that environment. This includes secure storage (even a locked drawer or file box), rules about who can see their screen during video calls, and proper document destruction methods.
Establish protocols for transporting documents between office and home. Many organizations prohibit this entirely. If it’s necessary for your business, require encrypted portable storage for digital files and specific cases or bags for physical documents. Documents should never be visible during transport.
Address the coffee shop problem. Some employees work from public spaces. Create clear rules: no sensitive documents in public locations, privacy screens required on laptops when working with confidential information, and VPN use mandatory for any data access.
Your protect sensitive documents at work policy needs to cover shared workspaces and hot-desking environments. When employees don’t have assigned desks, secure storage becomes even more critical. Provide lockers or secure areas where people can store materials during the workday and take sensitive items with them at the end of each day.
Measuring Success and Maintaining Momentum
How do you know if your clean desk policy is actually working?
Start with compliance metrics. Track the percentage of desks that are clean during spot checks. Your goal should be 95% or higher compliance within six months of implementation. Anything less suggests the policy needs adjustment or training needs reinforcement.
Monitor security incidents. Track reported cases of missing documents, unauthorized access to information, or other physical security breaches. A successful clean desk policy should reduce these incidents over time.
Survey your employees. Ask them if they understand the policy, whether they have the resources they need to comply, and what obstacles they face. This feedback helps you improve the policy and address practical implementation challenges.
Watch for policy drift. Over time, enforcement tends to relax and exceptions multiply. Schedule quarterly reviews to ensure the policy is being followed as written. Reset expectations when needed.
Conduct annual security assessments. Bring in an outside perspective (or have someone from another department) evaluate your physical security. Fresh eyes often spot issues that have become invisible to people who see them every day.
Document your wins. When your clean desk policy prevents a potential breach or protects sensitive information during an incident, document it. These case studies reinforce why the policy matters and justify continued investment in physical security measures.
Conclusion
Your cybersecurity is only as strong as your weakest physical security control. A clean desk policy isn’t about being neat. It’s about protecting the sensitive information that keeps your business running and your clients trusting you.
The reality is simple: digital security measures can’t protect information that’s sitting visible on a desk or left in an unlocked drawer. You can have the most sophisticated network security in your industry, but it means nothing if someone can walk through your office and photograph confidential documents.
Implementation takes effort. You’ll need to invest in secure storage, train your team, and maintain consistent enforcement. Some employees will resist at first. They’ll say it’s inconvenient or unnecessary. But when you explain the real risks and make compliance easy, most people get on board.
The businesses that get physical security right don’t treat it as an afterthought or a burden. They recognize it as a fundamental component of their overall security strategy. They build habits, create systems, and maintain them consistently.
Start today. Walk through your office and identify the physical security gaps. Draft your policy. Get the storage solutions you need. Train your team. Then follow through with the monitoring and enforcement that makes it stick.
Your sensitive documents, your competitive advantages, and your clients’ trust are worth protecting. A clean desk policy is one of the simplest and most effective ways to do it.
Key Takeaways
- Physical security failures account for 12% of all confirmed data breaches, often providing the easiest path for attackers to access sensitive information.
- A clean desk policy requires all sensitive documents to be secured in locked storage at the end of each workday and during extended absences.
- Successful implementation depends on making compliance easy through adequate storage solutions, clear definitions of sensitive materials, and practical training.
- Spot checks and progressive discipline maintain policy adherence, but systemic problems need systemic solutions rather than individual punishment.
- Hybrid work environments require extended policies covering home offices, document transport, and work in public spaces.
- Compliance should reach 95% or higher within six months, measured through regular audits and tracked security incidents.
Citations
- Verizon, “2024 Data Breach Investigations Report,” 2024.
- IBM Security, “Cost of a Data Breach Report 2024,” 2024.