Policies aren't bureaucracy. They're the rules of engagement that protect your business. But most SMBs either have none or haven't updated theirs in years.
I’ll be honest with you. When I started working with small businesses on cybersecurity, I expected to find outdated policies. What I actually found was worse: nothing at all.
Most small business owners I talk to assume cybersecurity policies are something only Fortune 500 companies need. They picture thick binders gathering dust on executive shelves. But here’s the reality: policies are not bureaucratic theater. They’re the difference between recovering from a breach and losing everything.
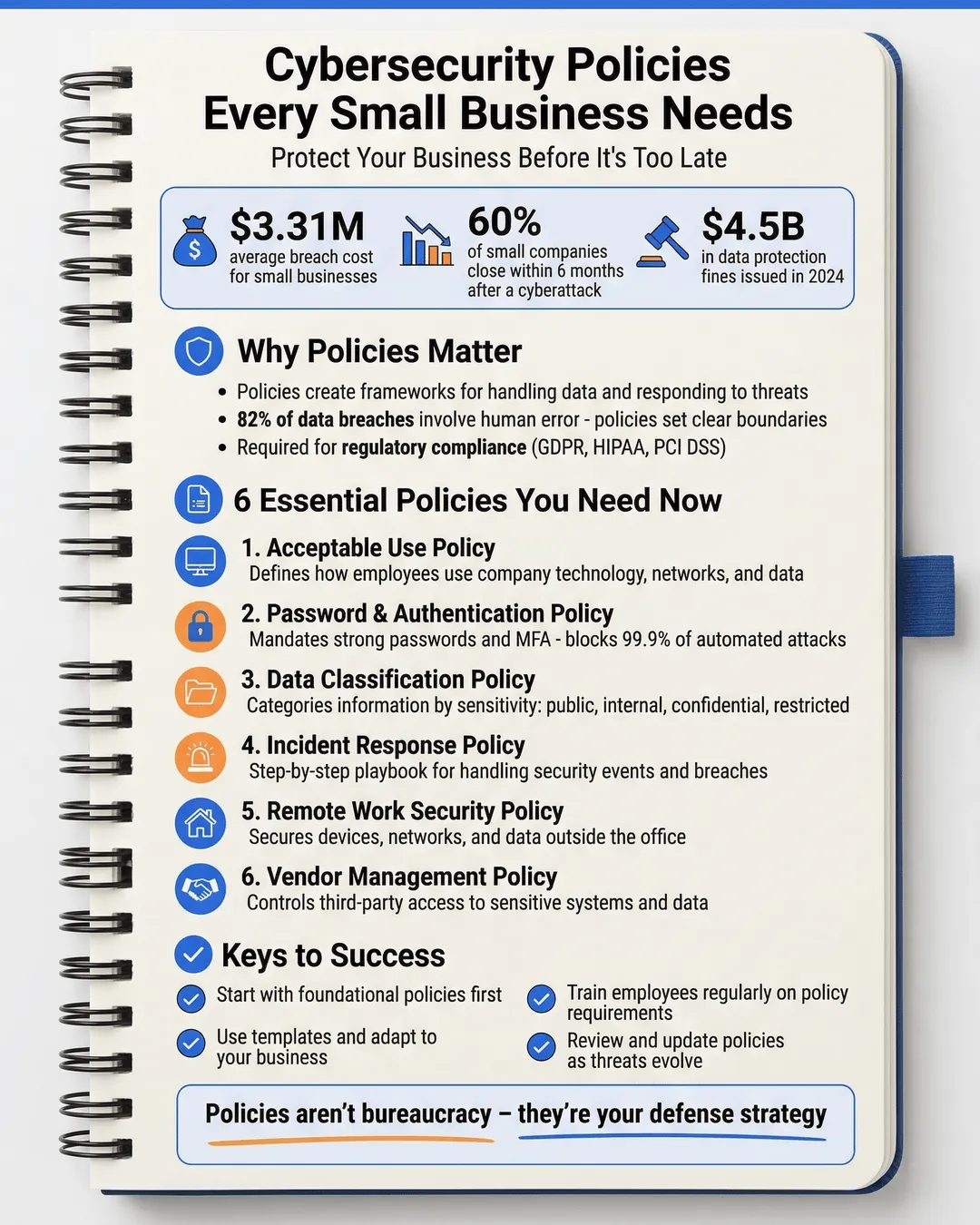
According to IBM’s 2024 Cost of a Data Breach Report, small businesses face an average breach cost of $3.31 million¹. And 60% of small companies that suffer a cyberattack go out of business within six months². Those are not scare tactics. Those are the stakes.
The good news? You don’t need a legal team or a six-figure budget to protect your business. You need clear, practical cybersecurity policies that your team actually follows.
Key Takeaways
- Cybersecurity policies provide clear rules that protect your business data, reduce human error, and ensure regulatory compliance.
- Essential policies include acceptable use, password management, data classification, incident response, remote work security, and vendor management.
- Policies only work if employees understand and follow them through regular training and updates.
- Start with foundational policies and adapt templates to your business rather than creating everything from scratch.
- Regular reviews and updates keep policies relevant as technology and threats evolve.
Why Cybersecurity Policies Matter More Than You Think
Let me paint you a picture. Your employee clicks a phishing link. They panic and close their laptop, hoping the problem disappears. Three weeks later, you discover ransomware has encrypted your customer database.
Could a policy have prevented this? Maybe not the initial click. But a solid incident response policy would have meant your employee reported it immediately. Your IT team could have contained the damage within hours instead of weeks.
That’s what policies do. They create a framework for how your business handles data, responds to threats, and maintains security standards. They turn chaos into process.
Beyond incident response, policies establish expectations. Your team knows what’s allowed and what’s not. They understand why certain rules exist. And when everyone follows the same playbook, your security posture strengthens dramatically.
Regulations also demand it. Depending on your industry, you may need policies to comply with GDPR, HIPAA, PCI DSS, or state privacy laws. In 2024, regulators issued over $4.5 billion in fines for data protection violations³. Policies demonstrate you’re taking reasonable steps to protect sensitive information.
The Essential Cybersecurity Policies Every Small Business Needs
You don’t need twenty policies. You need the right ones. Here are the foundational policies that protect most small businesses.
Acceptable Use Policy
This policy defines how employees can use company technology, networks, and data. It covers everything from personal device usage to social media access on company time.
Your acceptable use policy should specify what’s permitted and what’s prohibited. Can employees check personal email on work devices? Can they install software without approval? Can they use company equipment for side projects?
Clear boundaries prevent security gaps. Research shows that 82% of data breaches involve human error⁴. Many of those errors happen because employees didn’t know the rules.
Include consequences for violations. If someone repeatedly ignores the policy, what happens? Make expectations crystal clear.
Password and Authentication Policy
Weak passwords remain one of the easiest entry points for attackers. Your password policy should mandate minimum requirements: length, complexity, and regular updates.
But here’s where most businesses get it wrong. They create impossible requirements that force employees to write passwords on sticky notes. Instead, focus on length over complexity. A 16-character passphrase beats an 8-character jumble of symbols every time.
Require multi-factor authentication for all critical systems. Email, financial software, customer databases—everything important needs that second verification step. In 2024, MFA blocked 99.9% of automated attacks⁵.
Consider using a password manager for your team. It generates strong passwords, stores them securely, and removes the temptation to reuse credentials across multiple sites.
Data Classification and Handling Policy
Not all data deserves the same protection. Your company’s lunch order doesn’t need the same security as your customer payment information.
A data classification policy categorizes information by sensitivity level. Common categories include public, internal, confidential, and restricted. Each level gets specific handling requirements.
For example, restricted data might require encryption at rest and in transit, limited access controls, and audit logging. Internal data might only need basic access controls.
This approach focuses your security resources where they matter most. Your team also understands which information requires extra care.
Incident Response Policy
When something goes wrong, panic is the enemy. An incident response policy provides a step-by-step playbook for handling security events.
Define what constitutes an incident. Lost laptop? Suspicious email? Ransomware infection? Your team needs to know when to sound the alarm.
Outline the response process: who to contact, how to contain the threat, when to involve law enforcement, and how to communicate with customers if needed.
Assign specific roles. Who leads the response? Who handles technical remediation? Who manages external communications? Clear responsibilities prevent confusion during a crisis.
Practice your incident response plan annually. Run tabletop exercises where you simulate different scenarios. You’ll discover gaps in your policy before they matter.
Remote Work and BYOD Policy
Remote work is not going away. In 2024, 28% of employees worked remotely at least part-time⁶. Each remote connection is a potential security risk.
Your remote work policy should require VPN usage for accessing company resources, mandate endpoint protection on all devices, and prohibit public Wi-Fi for sensitive work.
If you allow employees to use personal devices for work (BYOD), that needs its own policy section. Specify security requirements: updated operating systems, approved apps only, remote wipe capability if the device is lost.
Define what happens when employment ends. How do you ensure company data gets removed from personal devices? Plan for it upfront.
Vendor and Third-Party Management Policy
Your security is only as strong as your weakest vendor. In 2024, 45% of breaches involved third-party vendors⁷.
A vendor management policy requires security assessments before onboarding new partners. What data will they access? How do they protect it? Do they have cyber insurance?
Include contractual security requirements. Your vendors should agree to specific security standards, breach notification timelines, and regular security audits.
Maintain an inventory of all third-party connections. Review it quarterly. Remove vendors you no longer use and reassess security for those you keep.
How to Implement Policies Your Team Will Actually Follow
Beautiful policies sitting in a shared drive help nobody. Implementation determines success.
Start with education. Before rolling out any policy, explain why it exists. Connect the rules to real risks. When employees understand the reasoning, they’re more likely to comply.
Keep policies readable. Write in plain language. If your policy requires a legal dictionary to understand, rewrite it. Aim for clarity over formality.
Make compliance easy. If your password policy requires complex passwords but you don’t provide a password manager, you’re setting your team up to fail. Remove friction wherever possible.
Designate a policy owner for each document. That person answers questions, tracks compliance, and recommends updates. Without ownership, policies stagnate.
Require annual acknowledgment. Every employee should review and acknowledge policies at least once per year. New hires should review them during onboarding.
Create quick-reference guides. Distill each policy into a one-page cheat sheet. Put these where employees actually work: in Slack channels, on the intranet, in email signatures.
Monitor compliance without becoming Big Brother. Automated tools can flag policy violations like weak passwords or unauthorized software installations. Use these as teaching opportunities, not punishment.
Getting Started: Your Action Plan
Feeling overwhelmed? Don’t be. You don’t need to create everything at once.
Start with three policies: acceptable use, password management, and incident response. These cover the most common security gaps for small businesses.
Use templates as starting points. Organizations like SANS Institute and NIST offer free cybersecurity policy templates⁸. Adapt them to your business rather than starting from scratch.
Involve your team in policy creation. They’ll offer insights into what’s practical and what’s not. Policies designed in a vacuum often fail in practice.
Set a review schedule. Commit to reviewing each policy annually. Technology changes. Threats evolve. Your policies should too.
Track incidents and near-misses. When something goes wrong (or almost does), review whether your policies would have prevented it. Update accordingly.
Consider getting help for the first round. A cybersecurity consultant can review your specific risks and recommend appropriate policies. Many insurance companies also offer free policy templates as part of cyber insurance coverage.
Document everything. Even informal security practices should be written down. You can refine the language later, but capturing the process is step one.
Conclusion
Cybersecurity policies are not about checking compliance boxes. They’re about protecting what you’ve built.
I’ve watched businesses recover from serious incidents because they had clear policies. I’ve also watched others fail because they didn’t. The difference is not budget or company size. It’s preparation.
Your small business faces real threats every day. Phishing attacks, ransomware, insider threats, vendor breaches—the list goes on. Policies give you and your team the tools to defend against these risks.
Start today. Pick one policy. Write it down. Share it with your team. Then move to the next one.
Because the best time to create cybersecurity policies was five years ago. The second-best time is right now.
Citations
- IBM Security, “Cost of a Data Breach Report 2024,” 2024.
- National Cyber Security Alliance, “Small Business Cybersecurity Statistics,” 2024.
- DLA Piper, “GDPR Fines and Data Breach Survey 2024,” 2024.
- Verizon, “2024 Data Breach Investigations Report,” 2024.
- Microsoft, “Digital Defense Report 2024,” 2024.
- McKinsey & Company, “American Opportunity Survey,” 2024.
- Ponemon Institute, “Third-Party Risk Management Study,” 2024.
- SANS Institute, “Information Security Policy Templates,” 2024.