Writing a cybersecurity policy is the easy part. Getting your team to read it, understand it, and follow it is the real challenge.
You spent weeks crafting a comprehensive cybersecurity policy. You covered password requirements, device protocols, data handling procedures, and incident response plans. You had legal review it. You formatted it beautifully. You sent it to everyone with a bold subject line.
And then… crickets.
Two months later, someone clicks a phishing link. Another employee shares login credentials with a contractor. Your marketing intern posts sensitive company data in a public Slack channel. When you bring up the policy, you get blank stares.
Sound familiar?
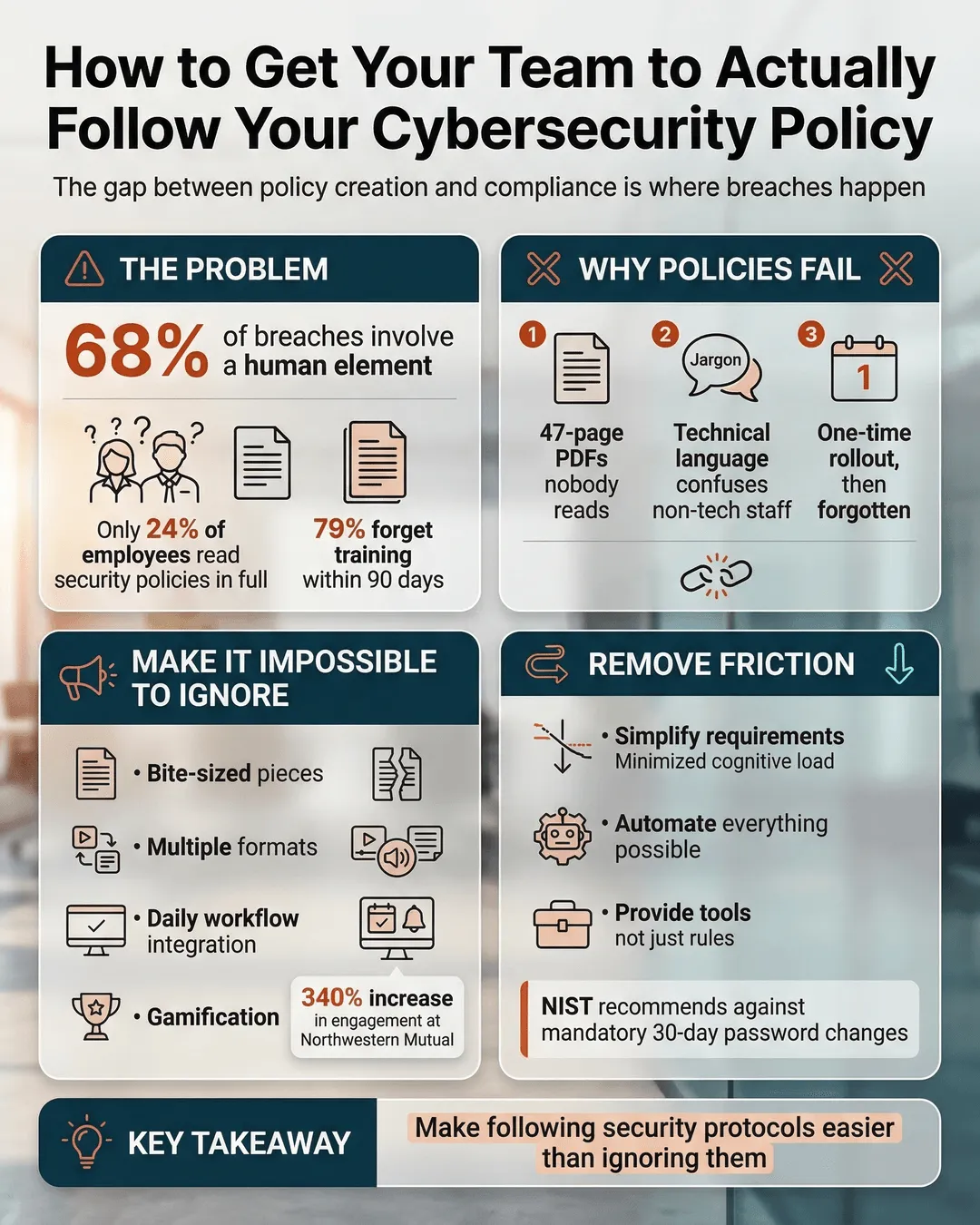
Creating a cybersecurity policy is straightforward. Getting your team to actually read it, internalize it, and follow it consistently requires a completely different skill set. The gap between policy creation and policy compliance is where most security breaches happen. According to Verizon’s 2024 Data Breach Investigations Report, 68% of breaches involve a human element¹.
Let’s fix that gap.
Key Takeaways
- Treat your cybersecurity policy like a product launch, not a compliance checkbox.
- Break policies into digestible formats and deliver them where employees already spend time.
- Make following security protocols easier than ignoring them through automation and simplified processes.
- Use real consequences and real rewards to reinforce compliant behavior.
- Measure what matters with specific metrics and adjust based on actual employee behavior.
Why Your Current Approach Is Not Working
Before we talk solutions, let’s address why most cybersecurity policies fail to stick.
You probably did what everyone does. You created a 47-page PDF, sent it via email with “IMPORTANT: READ IMMEDIATELY” in the subject line, asked everyone to acknowledge receipt, and called it done. Maybe you even required a digital signature.
Here’s the problem. Nobody reads 47-page PDFs. A study by SecurityAdvisor found that only 24% of employees read their company’s security policy in full².
Your employees are busy. They’re juggling deadlines, meetings, projects, and personal responsibilities. When they see a massive policy document, their brains immediately categorize it as “something to deal with later.” Later never comes.
Even worse, traditional policies use language written by lawyers for lawyers. Terms like “multifactor authentication,” “endpoint security,” and “zero-trust architecture” mean nothing to your sales team or customer service reps. The disconnect between technical jargon and everyday language creates confusion. Confusion creates non-compliance.
You also probably rolled out the policy once and never mentioned it again. Security awareness is not a one-and-done activity. Research from KnowBe4 shows that employees forget 79% of security training within 90 days³.
Make It Impossible to Ignore (In a Good Way)
To enforce cybersecurity policy effectively, you need to meet employees where they are, not where you wish they would be.
Break the policy into bite-sized pieces. Nobody wants to read 47 pages, but everyone can handle a two-minute read. Split your policy into short, focused sections. Create individual documents for password management, phishing recognition, device security, and data handling. Each section should address one topic and fit on a single page.
Use multiple formats. Some people learn by reading. Others prefer video or interactive content. Create short video explainers for key policies. Develop quick-reference checklists. Design infographics that highlight the most important rules. Record brief audio explanations for employees who commute or multitask.
Integrate security reminders into daily workflows. Do not rely on employees to remember your policy. Build reminders directly into the tools they use every day. Add security tips to your email signatures. Create Slack bots that share weekly security reminders. Display rotating security messages on login screens. Place physical reminders near printers and in conference rooms.
Gamify awareness. Turn security education into something people actually want to participate in. Launch a monthly security quiz with small prizes for top scorers. Create a points system where employees earn rewards for reporting phishing attempts or completing training modules. Run simulated phishing campaigns and publicly celebrate (not shame) teams with the best detection rates.
Northwestern Mutual implemented a gamified security program and saw employee engagement in security training increase by 340%⁴.
Remove Friction and Make Compliance the Path of Least Resistance
People follow the easiest path. If ignoring your policy is easier than following it, they will ignore it.
Simplify your requirements. Review every policy requirement and ask, “Is this absolutely necessary?” Every additional rule increases cognitive load and reduces compliance. Cut anything that does not directly reduce risk. For example, if you require password changes every 30 days, you are creating frustration without meaningful security gains. NIST now recommends against mandatory periodic password changes unless there is evidence of compromise⁵.
Automate wherever possible. The best security policy is the one employees do not have to think about. Use password managers so employees do not have to memorize complex passwords. Implement single sign-on to reduce login fatigue. Enable automatic software updates. Deploy mobile device management that enforces encryption without user intervention. Set up email filters that flag suspicious messages before they reach inboxes.
Provide tools, not just rules. If you require encrypted file sharing, provide an easy-to-use encrypted sharing platform. If you mandate two-factor authentication, choose a solution that works seamlessly with your existing systems. If you prohibit personal email for work files, give employees a better alternative.
Create decision trees for common scenarios. Employees often violate policies because they do not know what to do in specific situations. Build simple flowcharts that answer questions like, “Can I work from this coffee shop?” or “Should I click this link from our vendor?” Make these visual guides accessible through a quick link on your intranet or a pinned message in your team chat.
Dropbox reduced security incidents by 60% after implementing simplified security workflows and removing unnecessary friction points⁶.
Make It Personal and Real
Abstract threats do not motivate behavior change. Real stories and tangible consequences do.
Share real examples. Use actual case studies of breaches that happened to companies like yours. If possible, share sanitized examples from your own organization. When employees see how a single clicked link led to a ransomware attack that shut down operations for three days, the threat becomes real.
Explain the “why” behind each rule. Do not just tell employees they cannot use public Wi-Fi for work. Explain that unsecured networks allow attackers to intercept sensitive data, which could expose customer information and put the company at legal risk. When people understand the reasoning, they are more likely to comply.
Connect security to personal impact. Frame security practices in terms of how they protect employees, not just the company. A data breach does not just hurt the business. It can expose employee personal information, social security numbers, and banking details. Make it clear that following security protocols protects their own data and privacy.
Assign accountability at every level. Security cannot be just an IT department responsibility. Every manager should be responsible for their team’s security compliance. Include security metrics in performance reviews. Make department heads report on their team’s completion rates for security training. When accountability is distributed, compliance improves.
Implement consequences for violations. This does not mean firing someone for their first mistake. It means having a clear, fair process for handling non-compliance. First offense might be additional training. Second offense could involve a formal conversation with HR. Repeated, willful violations should carry real consequences. Equally important, enforce these consequences consistently across all levels of the organization. If executives get a pass, everyone else will too.
Measure, Monitor, and Adapt
You cannot improve what you do not measure. To enforce cybersecurity policy effectively, you need data on what is actually happening.
Track meaningful metrics. Monitor phishing simulation click rates, security training completion rates, password manager adoption, two-factor authentication enrollment, and incident response times. Review these metrics monthly and look for trends.
Conduct regular surveys. Ask employees what security practices they find confusing or difficult. Find out which tools they struggle with. Discover which policies they think are unnecessary. This feedback will reveal gaps between policy and practice.
Run spot audits. Periodically check whether policies are being followed. Review a random sample of devices to verify encryption is enabled. Check shared drives for improperly stored sensitive data. Examine email practices to ensure confidential information is not being sent insecurely. Use findings to identify training opportunities, not to punish.
Test your incident response plan. Run tabletop exercises where teams walk through what they would do if a breach occurred. These simulations reveal whether employees actually know how to report incidents, who to contact, and what steps to take. They also reinforce the importance of following protocols.
Update policies based on reality. If everyone ignores a particular policy, you have two options. Either make the policy easier to follow, or remove it. Policies that exist only on paper create a false sense of security and train employees that compliance is optional.
Cisco’s Security Outcomes Study found that organizations that regularly measure and adapt their security programs are 3.5 times more likely to achieve their security goals⁷.
Build a Culture Where Security Is Everyone’s Job
Long-term compliance requires a shift from viewing security as an IT problem to making it part of your organizational culture.
Start from the top. If your CEO ignores security policies, everyone else will too. Leadership must visibly follow every security protocol. When executives use password managers, enable two-factor authentication, and report suspicious emails, it sends a powerful message. Make security a standing agenda item in leadership meetings.
Celebrate security wins. Publicly recognize employees who report phishing attempts, identify vulnerabilities, or suggest security improvements. Share stories in company newsletters, team meetings, and Slack channels. Create a “Security Champion” program where employees from different departments become go-to resources for security questions.
Make security easy to discuss. Create channels where employees can ask security questions without fear of judgment. Set up a dedicated Slack channel or email address where people can report concerns or ask for clarification. Respond quickly and helpfully. The easier you make it to ask questions, the less likely employees are to make dangerous assumptions.
Integrate security into onboarding. New employees should receive security training on day one, not week six. Make it part of the standard onboarding process alongside benefits enrollment and equipment setup. Assign new hires a security mentor who can answer questions during their first few weeks.
Regularly refresh training. Annual security training is not enough. Implement quarterly micro-training sessions that take 10 minutes or less. Focus each session on one specific topic. Mix up the format to keep things engaging. Use current events and recent breaches as teaching moments.
Conclusion
Getting your team to actually follow your cybersecurity policy is not about creating perfect documents or implementing draconian enforcement. It is about understanding human behavior and designing systems that make compliance natural, easy, and consistent.
Break your policy into digestible pieces. Remove friction from security processes. Make threats tangible and personal. Measure what matters and adapt based on real behavior. Build a culture where security is everyone’s responsibility, not just a checkbox exercise.
Your policy is only as strong as your team’s willingness and ability to follow it. Invest the same energy into implementation and enforcement that you invested in creation. Your security posture depends on it.
Citations
- Verizon, “2024 Data Breach Investigations Report,” 2024.
- SecurityAdvisor, “Employee Security Policy Engagement Study,” 2024.
- KnowBe4, “Security Awareness Training Retention Research,” 2024.
- Northwestern Mutual, “Gamification in Security Training Case Study,” 2024.
- National Institute of Standards and Technology, “Digital Identity Guidelines,” 2024.
- Dropbox, “Security Workflow Optimization Report,” 2024.
- Cisco, “Security Outcomes Study,” 2024.