After a cyberattack, many business owners do not know who to call or what to report. Timely reporting can limit damage and fulfill legal requirements.
You just discovered that your business suffered a cyberattack. Your heart is racing. Your mind is spinning with questions. And the biggest question of all: who do you call?
Most small business owners spend weeks preparing cybersecurity defenses but zero time planning what happens after an attack. When ransomware locks up your files or a data breach exposes customer information, knowing how to report a cyberattack becomes just as critical as having antivirus software.
Reporting a cyber incident isn’t just about doing the right thing. It’s about protecting your business from further damage, meeting legal obligations, and potentially stopping attackers from hitting other companies. This guide walks you through exactly who to contact, what information you need to provide, and when you need to act.
Key Takeaways
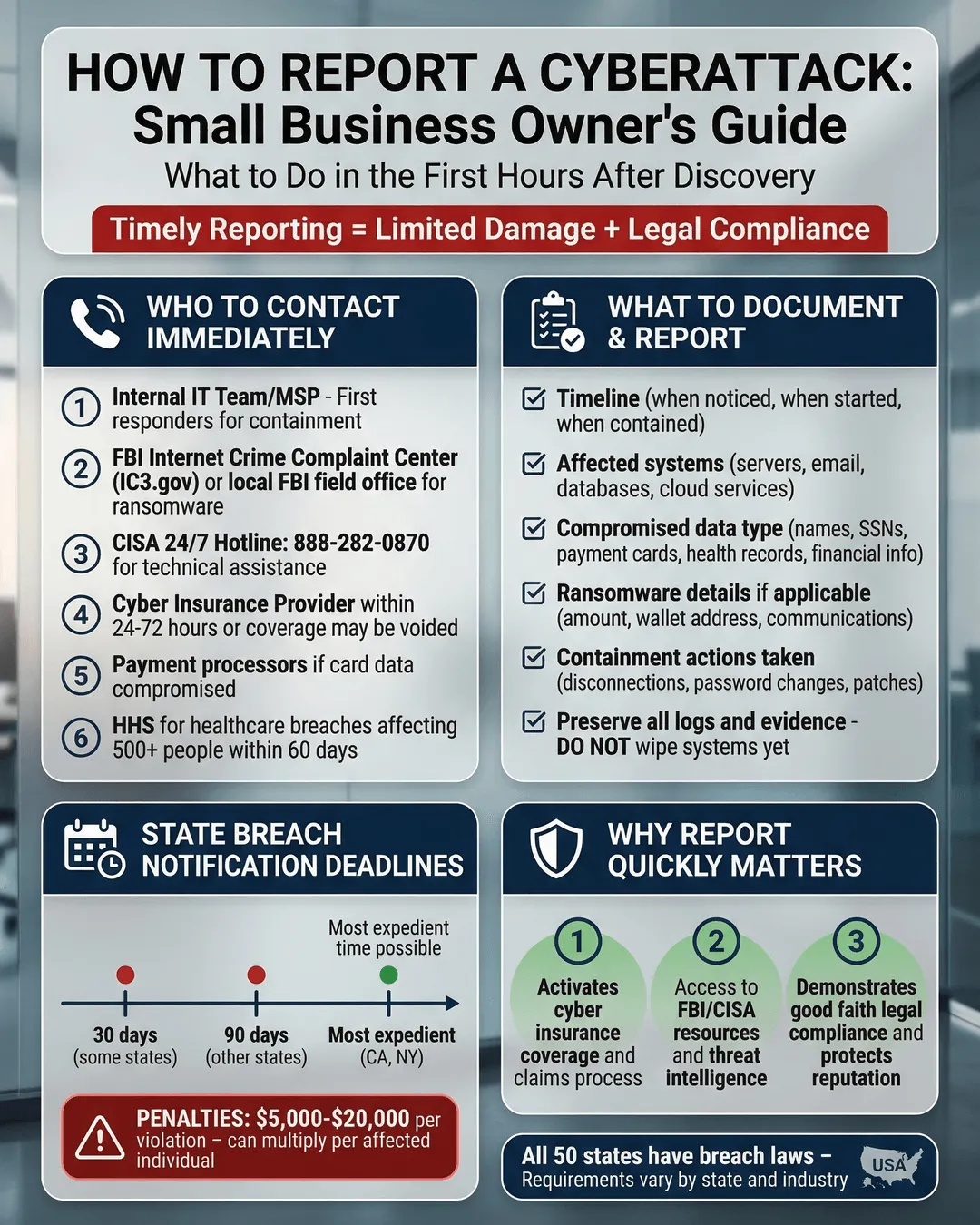
- Report cyberattacks to multiple parties including the FBI’s Internet Crime Complaint Center, your local FBI field office for serious incidents, and relevant regulatory agencies based on your industry.
- Document everything immediately including the time you discovered the attack, what systems were affected, and any communications from attackers before contacting authorities.
- Notify customers and partners within legally required timeframes, which vary by state and can be as short as 72 hours after discovering a data breach.
- Contact your cyber insurance provider within 24 hours of discovering an attack to ensure coverage and access incident response resources.
- Preserve all evidence including logs, screenshots, and ransom notes as law enforcement may need this information to investigate and potentially recover your data.
Who to Call First After Discovering a Cyberattack
The moments after discovering a cyberattack feel chaotic. You need a clear action plan.
Start by isolating affected systems to prevent the attack from spreading. Disconnect compromised computers from your network, but do not power them down completely. Law enforcement and forensic teams need to examine those systems in their current state.
Your first call should go to your internal IT team or managed service provider. They can confirm the attack, assess the scope, and begin containment. If you don’t have dedicated IT staff, contact a cybersecurity incident response firm immediately.
Next, call your cyber insurance provider. Most policies require notification within 24 hours of discovering an incident¹. Your insurer can also connect you with pre-approved forensic investigators and legal counsel, which saves precious time.
For serious attacks involving ransomware, data theft, or financial loss, contact the FBI. You have two reporting options. File a complaint with the Internet Crime Complaint Center at ic3.gov for all types of cybercrime. This online portal accepts reports 24/7 and helps the FBI track cybercrime trends². For active ransomware attacks or significant breaches, call your local FBI field office directly. They can provide guidance and potentially intervene if the attackers are part of a known criminal group.
Do not skip law enforcement reporting because you feel embarrassed or think nothing can be done. The FBI recovered over $500 million for ransomware victims in 2024³. They cannot help if they don’t know about your situation.
Understanding Your Legal Reporting Requirements
Cyber incident reporting requirements vary based on your industry, location, and the type of data compromised.
All 50 states have data breach notification laws, but the specifics differ wildly. Some states require notification within 30 days, others demand action within 72 hours⁴. If you operate in multiple states or serve customers nationwide, you must comply with the strictest applicable law.
California’s breach notification law serves as a common baseline. You must notify affected individuals “without unreasonable delay” and no later than when you notify law enforcement⁵. That creates a tight timeline once you confirm customer data was accessed.
Certain industries face additional requirements. Healthcare organizations must report breaches affecting 500 or more individuals to the Department of Health and Human Services within 60 days⁶. Financial institutions must notify their primary federal regulator as soon as possible, and no later than 36 hours after determining a significant incident occurred⁷.
Even if no specific regulation applies to your business, you may have contractual obligations. Review your customer agreements, vendor contracts, and payment processor terms. Many include breach notification clauses with specific timeframes.
The consequences for failing to report get expensive. State attorneys general can impose fines ranging from $2,500 to $7,500 per violation⁸. That means each affected customer whose notification you delay could trigger a separate penalty.
Create a reporting checklist now, before an attack happens. Identify which agencies oversee your industry, review your state’s notification timeline, and note any contractual requirements. This preparation makes compliance automatic during a crisis.
How to Report a Data Breach to the Right Agencies
Reporting a cyberattack to authorities requires more than just picking up the phone. You need to provide specific information and follow proper channels.
When you report a ransomware attack to the FBI through the Internet Crime Complaint Center, include the ransom note text, the attackers’ contact information or payment wallet addresses, and a description of how the attack occurred. The FBI uses this data to identify attack patterns and track criminal groups. You can file a report at ic3.gov without needing to speak with anyone if you prefer written documentation.
For incidents involving financial fraud or business email compromise, the IC3’s Recovery Asset Team works to freeze fraudulent transactions. The faster you report, the better their chances of recovering your funds. Reports filed within 72 hours have significantly higher recovery rates⁹.
State attorneys general also need notification when resident data gets compromised. Most states accept electronic notification through their official websites, but some require physical mail. Check your state AG’s website for specific submission requirements. You typically need to provide the number of residents affected, the types of data compromised, and the date you discovered the breach.
Industry regulators have their own reporting portals. Healthcare organizations report through the HHS HIPAA Breach Reporting Tool. Financial institutions use their regulatory agency’s designated system. The SEC requires publicly traded companies to disclose material cybersecurity incidents within four business days¹⁰.
When you report, stick to facts. Describe what happened, what data was affected, and what steps you took to contain the incident. Avoid speculation about who attacked you or why. Law enforcement will investigate the technical details.
Keep copies of every report you file. Document the date, time, agency, and confirmation number for each submission. This record proves compliance if questions arise later.
What Information You Need to Document and Report
The quality of your incident report matters as much as the speed.
Start documenting the moment you suspect an attack. Write down when you first noticed unusual activity, who discovered it, and what they observed. Take screenshots of ransom notes, suspicious emails, or error messages before they disappear.
Your incident report should include several key elements. Describe the attack timeline including when the incident likely began (based on log files), when you discovered it, and when you contained it. List all affected systems, applications, and data types. Specify how many individuals had their information exposed and what categories of data were compromised such as names, social security numbers, financial account numbers, or health records.
Preserve all digital evidence. Make forensic copies of affected hard drives before making any changes. Save server logs, firewall logs, and email headers. These artifacts help investigators track the attack source and method.
Do not delete anything, even if it looks like the attack vector. That suspicious email attachment or infected file contains clues about how attackers gained access. Removing evidence makes investigation harder and might violate legal preservation requirements if litigation follows.
Document your response actions. Note what steps you took to contain the attack, which vendors or consultants you engaged, and what security improvements you implemented. This information demonstrates your good faith effort to address the incident, which matters if regulators review your response.
For ransomware attacks, never pay the ransom before reporting to law enforcement. The FBI and CISA strongly discourage ransom payments because they fund criminal operations and offer no guarantee of data recovery¹¹. Report first, then make an informed decision with your legal counsel and incident response team.
Notifying Customers, Partners, and the Public
After you report to authorities, you need to tell the people whose data was compromised.
Customer notification must be clear, specific, and actionable. Your notice should explain what happened in plain language, what types of information were exposed, what steps you have taken to address the incident, and what actions customers should take to protect themselves.
Provide concrete guidance. If social security numbers were stolen, recommend credit monitoring and fraud alerts. If login credentials were compromised, require immediate password resets. Vague statements like “we take security seriously” do not help anyone.
Timing matters enormously. Many state laws require notification within a specific window after you discover the breach. Calculate this timeline from when you confirm unauthorized access occurred, not from when the attack started. If forensic investigation takes three weeks to verify what data was accessed, the clock starts when that verification completes.
Choose appropriate notification methods based on the number of people affected and the information available. Direct notification by email or postal mail works for incidents affecting a defined group of individuals. For widespread breaches where contact information is incomplete, supplement with substitute notice through your website, major media outlets, or statewide publication.
Business partners and vendors need notification too, especially if the attack exposed their data or compromised systems you share with them. Check your vendor agreements for notification requirements. Many B2B contracts specify shorter timeframes than state consumer protection laws.
Consider hiring a breach notification service to manage mass communications. These firms specialize in compliant notification letters, call center support, and credit monitoring enrollment. The cost is significant, but the alternative is trying to manage thousands of customer inquiries while recovering from an attack.
Public disclosure depends on your situation. Publicly traded companies must file incident disclosures with the SEC. Other businesses should consult legal counsel before making public statements. What you say publicly can be used against you in litigation or regulatory enforcement.
Your reputation takes a hit after a breach regardless of how you communicate. Transparency and swift action minimize the damage. Customers respect organizations that acknowledge problems and explain their response more than companies that hide or downplay incidents.
Conclusion
Knowing how to report a cyberattack before you need to can make the difference between a contained incident and a business-ending disaster.
Create your reporting plan today. List the phone numbers for your FBI local field office, your state attorney general, and your industry regulator. Add your cyber insurance provider’s emergency contact and your incident response vendor. Put these numbers somewhere you can access them during a crisis, like a printed sheet in your desk and a note on your phone.
Review your state’s data breach notification requirements and mark the deadline on your incident response checklist. Identify which types of data trigger notification requirements for your business. Discuss your legal obligations with your attorney now, not after an attack.
Most importantly, do not let fear of reporting stop you from getting help. Law enforcement, regulators, and industry groups want to help small businesses recover from cyberattacks. The sooner you report, the more options you have.
Cyberattacks will continue to target small businesses because attackers perceive them as easy targets with valuable data. Change that perception by being the business owner who knows exactly what to do when the worst happens.
Citations
- Insurance Information Institute, “Cyber Insurance Coverage and Claims Trends,” 2024.
- Federal Bureau of Investigation, “Internet Crime Complaint Center Annual Report,” 2024.
- Federal Bureau of Investigation, “Ransomware Recovery Statistics,” 2024.
- National Conference of State Legislatures, “Security Breach Notification Laws,” 2024.
- California Civil Code Section 1798.82, “Data Breach Notification Requirements,” 2024.
- U.S. Department of Health and Human Services, “HIPAA Breach Notification Rule,” 2024.
- Federal Financial Institutions Examination Council, “Computer-Security Incident Notification Requirements,” 2024.
- National Association of Attorneys General, “State Data Breach Enforcement Actions,” 2024.
- Federal Bureau of Investigation, “IC3 Recovery Asset Team Success Rates,” 2024.
- Securities and Exchange Commission, “Cybersecurity Risk Management Rule,” 2023.
- Cybersecurity and Infrastructure Security Agency, “Ransomware Response Guidance,” 2024.