Your Quarterly Phishing Test Isn't a Cybersecurity Strategy (And Your Team Knows It)
We need to talk about something that’s been bothering us for a while now. Too many small and medium-sized businesses think they’ve got cybersecurity awareness covered because they send out a phishing quiz every three months and call it a day.
Let’s be honest. That’s not a cybersecurity awareness program. That’s a checkbox exercise.
We’ve watched countless SMB leaders congratulate themselves for meeting some baseline compliance requirement while their employees click on malicious links, reuse passwords across systems, and plug random USB drives into company computers. The disconnect is staggering.
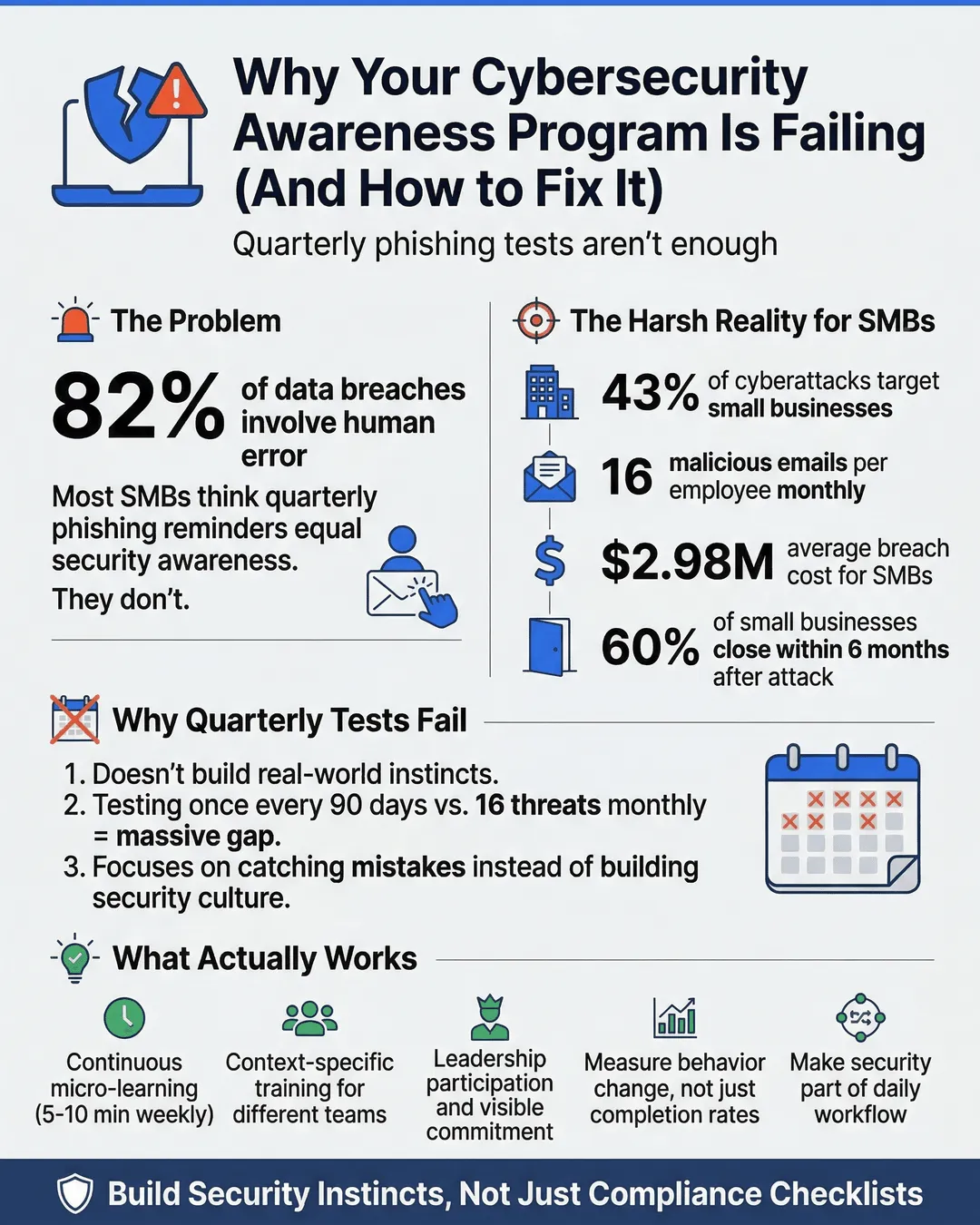
Here’s the reality: 82% of data breaches involve a human element¹. That means your people are either your strongest defense or your biggest vulnerability. Quarterly phishing tests aren’t going to cut it when your team faces sophisticated social engineering attacks daily.
The good news? We can fix this. But first, we need to understand why the current approach fails so spectacularly.
Key Takeaways
- Quarterly phishing tests create a false sense of security without building genuine cyber awareness
- Effective cybersecurity awareness requires continuous learning, not sporadic reminders
- SMBs face the same sophisticated threats as large enterprises but often lack dedicated security teams
- Context-specific training that relates to employees’ actual workflows drives better retention and behavior change
- Leadership participation and visible commitment to security culture matters more than any single training module
- Micro-learning approaches (5-10 minute sessions) prove more effective than annual compliance marathons
- Measuring behavioral change over time provides better insights than test completion rates
The Quarterly Phishing Test Illusion
We send out a simulated phishing email. Some people click it. We send them a scolding message and make them watch a 20-minute video. Three months later, we repeat the process. Progress, right?
Wrong.
This approach fundamentally misunderstands how people learn and change behavior. Cybersecurity awareness isn’t about catching people making mistakes. It’s about building instincts and creating a culture where security becomes second nature.
Think about how you learned to drive. Did someone test you on road rules once a quarter and expect you to become a safe driver? No. You practiced continuously, received real-time feedback, and gradually built muscle memory for complex tasks like merging onto highways or parallel parking.
Cybersecurity works the same way. A quarterly test doesn’t build the mental models people need to spot a sophisticated spear-phishing attempt or recognize when a “urgent request from the CEO” doesn’t quite sound right.
The average employee receives 16 malicious emails per month². That’s roughly four potential security incidents per week. Your quarterly test prepares them for exactly none of those real-world scenarios.
We’re setting people up to fail, then blaming them when breaches happen.
What SMBs Actually Face in the Threat Landscape
Small and medium-sized businesses operate under a dangerous misconception: “We’re too small to be targeted.”
Let us shatter that illusion. 43% of cyberattacks target small businesses³. Attackers know SMBs often have weaker defenses, limited security budgets, and no dedicated IT security team. You’re not flying under the radar. You’re an easier target.
The threats your team encounters aren’t amateur hour anymore. Cybercriminals use the same AI-powered tools, sophisticated social engineering tactics, and professional-grade malware against SMBs as they do against Fortune 500 companies. The difference is that large enterprises have security operations centers monitoring for threats 24/7. You probably don’t.
Your accounting department receives an email that looks exactly like it came from your payroll provider, complete with correct logos, formatting, and seemingly legitimate domains. The email urgently requests updated banking information for direct deposit. Without proper awareness training, someone processes that request. Boom. Your next payroll goes straight to criminals.
Or consider this scenario: Your sales team uses a collaboration tool. An attacker compromises one account through credential stuffing (trying username/password combinations leaked from other breaches). Because your team shares documents freely within the platform, the attacker now has access to client data, pricing strategies, and internal communications. They lurk quietly for weeks, mapping your organization before launching a targeted attack.
These aren’t hypothetical scenarios. We see them play out constantly. The average cost of a data breach for an SMB is $2.98 million⁴. Most small businesses can’t absorb that hit. 60% of small companies go out of business within six months of a cyberattack⁵.
Your quarterly phishing test doesn’t prepare your team for these realities.
What Actually Works: Building Real Security Awareness
So what should you do instead? We’re glad you asked.
Effective cybersecurity awareness starts with understanding that security isn’t an IT problem. It’s a business problem that requires everyone’s participation. Here’s what that looks like in practice.
Make it continuous, not periodic. Shift from quarterly events to ongoing micro-learning. Send a five-minute security tip every week. Share real-world examples of current scams targeting your industry. Create bite-sized training modules people can complete during coffee breaks. The goal is to keep security top of mind, not to overwhelm people once a quarter.
Make it relevant, not generic. Your finance team faces different threats than your sales team. Your remote workers need different guidance than your office-based employees. Customize your awareness program to address the specific risks each group encounters in their daily work. When training feels applicable to someone’s actual job, they pay attention.
Make it behavioral, not informational. Knowing what a phishing email looks like doesn’t automatically change how someone responds under pressure. Focus on building better habits and decision-making processes. Teach people to pause before clicking, verify requests through alternate channels, and trust their instincts when something feels off. Practice these behaviors repeatedly until they become automatic.
Make it positive, not punitive. Stop treating security awareness as a “gotcha” game. When someone reports a suspicious email (even if it turns out to be legitimate), celebrate that vigilance. Create a culture where asking questions about security is encouraged, not mocked. People should feel safe admitting they made a mistake rather than hiding it and hoping nothing bad happens.
One SMB we worked with implemented “Security Champions” in each department. These weren’t IT people. They were volunteers from sales, finance, operations, and other teams who received extra training and became the first point of contact for security questions. This peer-to-peer model worked better than top-down mandates because people felt comfortable asking their colleagues for help.
Another company we know runs monthly “Security Office Hours” where anyone can drop in and ask the IT team questions about security topics, from “Is this email legitimate?” to “How do I use the password manager?” Making security accessible and approachable dramatically improved their security posture.
The key insight is this: security awareness is about building organizational muscle memory. You need consistent practice, immediate feedback, and gradual skill development. You can’t achieve that with quarterly tests any more than you could become fluent in a language with quarterly lessons.
The Role of Leadership in Security Culture
Here’s something that might make you uncomfortable: your security culture starts with you.
We’ve seen too many business leaders who delegate cybersecurity entirely to IT, then wonder why employees don’t take it seriously. If leadership doesn’t visibly prioritize security, why would anyone else?
This doesn’t mean you need to become a cybersecurity expert. It means you need to demonstrate that security matters through your actions. Use the password manager. Enable two-factor authentication. Follow the same protocols you expect from your team. Ask security questions in meetings. Allocate budget for security tools and training.
When employees see leadership cutting corners on security, they internalize that the rules don’t really matter. When they see leadership taking security seriously, they follow suit.
One CEO we know includes a “security spotlight” in every company all-hands meeting. Sometimes it’s celebrating an employee who reported a phishing attempt. Sometimes it’s discussing a recent breach in their industry and what they’re doing to prevent similar issues. Sometimes it’s just reinforcing why security matters to the business. This consistent messaging from the top shapes culture more effectively than any training module.
Leadership also needs to provide resources. A comprehensive cybersecurity awareness program requires investment. You need quality training content, security tools, potentially outside expertise, and employee time. Telling your team to “be more careful” without giving them the tools and knowledge to succeed is setting them up for failure.
Budget allocation sends a clear message about priorities. When you invest in security awareness training, employee assistance programs, and proper security infrastructure, you demonstrate that protecting the business and its people matters.
Measuring What Actually Matters
Most SMBs measure cybersecurity awareness through test completion rates and quiz scores. These metrics are easy to track but tell you almost nothing about your actual security posture.
Here’s what you should measure instead: behavioral change over time.
Track how many employees report suspicious emails. Monitor password hygiene improvements. Measure the time it takes for people to update software when prompted. Look at the reduction in security incidents. These indicators reveal whether your awareness program actually changes behavior.
We worked with a company that shifted their metrics from “percentage of employees who passed the phishing test” to “percentage of employees who reported suspicious emails within the first hour of receiving them.” This reframing changed everything. Suddenly, the goal wasn’t to avoid making mistakes. The goal was to actively contribute to organizational security.
They also started tracking “near misses” in addition to actual incidents. When someone almost fell for a scam but caught themselves or asked for help, that got documented and celebrated. This created a learning culture where mistakes became teaching opportunities rather than sources of shame.
Another useful metric is “time to remediation.” When a security issue is discovered (an unauthorized app, a weak password, outdated software), how quickly does the team address it? Fast remediation indicates that people understand why security matters and prioritize fixing issues.
You should also measure engagement with your security awareness program. Are people actually completing the training modules? Are they asking questions during office hours? Do they engage with your weekly security tips? Low engagement often indicates that your content isn’t resonating or that you’ve created too much friction in the process.
Survey your team regularly about their confidence in handling security situations. Ask questions like “How confident are you in identifying a phishing email?” or “Do you know what to do if you suspect your account has been compromised?” Track how these confidence levels change over time.
The goal isn’t to achieve 100% on any single metric. The goal is to see continuous improvement across multiple indicators, demonstrating that your security culture is maturing.
Building Your Better Cybersecurity Awareness Program
Ready to move beyond quarterly phishing tests? Here’s how to build something better.
Start with a baseline assessment. Before you can improve, you need to understand where you are. Conduct a security culture survey. Review your incident history. Identify your highest-risk areas and most vulnerable teams. This assessment guides your priorities.
Create a content calendar. Plan your security awareness activities for the next 12 months. Mix different formats: short tips, video tutorials, interactive scenarios, discussion forums, and yes, occasional phishing simulations. Variety maintains engagement and addresses different learning styles.
Tailor content to your industry and risks. Generic security training misses the mark. If you’re a healthcare company, focus on HIPAA compliance and patient data protection. If you’re in retail, emphasize payment card security. If you handle intellectual property, stress data classification and access controls. Make it relevant.
Implement just-in-time learning. Deliver training when people need it most. When someone’s about to share a document externally, provide a quick reminder about data sensitivity. When tax season approaches, warn about tax-related scams. Contextual learning sticks better than abstract instruction.
Make security tools easy to use. If your security measures create so much friction that people work around them, you’ve failed. Implement single sign-on to reduce password fatigue. Use password managers that integrate seamlessly with browsers. Choose security tools with intuitive interfaces. The easier you make secure behavior, the more likely people are to adopt it.
Create feedback loops. When someone reports a suspicious email, let them know whether it was actually malicious and thank them for their vigilance. When you implement a new security measure based on employee feedback, acknowledge that contribution. People engage more when they see their actions making a difference.
Partner with your IT team. Your IT or security team should be allies in building awareness, not enforcers of rules. Position them as resources and helpers, not police. Encourage them to explain the “why” behind security measures. When people understand the reasoning, they’re more likely to comply willingly.
Review and adapt regularly. Your threat landscape changes constantly. Your awareness program should evolve with it. Quarterly reviews of your program effectiveness, using the behavioral metrics we discussed earlier, help you identify what’s working and what needs adjustment.
Conclusion
Cybersecurity awareness isn’t a compliance checkbox. It’s a continuous process of building knowledge, changing behavior, and creating a culture where everyone takes responsibility for protecting the organization.
Your quarterly phishing test isn’t protecting you. It’s creating a false sense of security that might be worse than no program at all.
We understand the constraints SMBs face. Limited budgets, stretched resources, competing priorities. But here’s the thing: you can’t afford not to invest in proper security awareness. The cost of a breach, both financial and reputational, far exceeds the investment in building a strong security culture.
Start small if you need to. Pick one thing from this article and implement it this month. Next month, add another. Build momentum gradually. The perfect program you never implement is worse than the imperfect program you start today.
Your employees want to do the right thing. They don’t click on malicious links because they’re careless or stupid. They do it because they’re busy, distracted, and haven’t been given the tools and knowledge to recognize sophisticated threats.
Give them that knowledge. Make security accessible, relevant, and continuous. Lead by example. Measure what matters. Celebrate progress.
And please, retire the quarterly phishing test. Your organization deserves better.
Citations
- Verizon, “2024 Data Breach Investigations Report,” 2024.
- Symantec, “Internet Security Threat Report,” 2024.
- Accenture, “Cost of Cybercrime Study,” 2024.
- IBM Security, “Cost of a Data Breach Report 2024,” 2024.
- National Cyber Security Alliance, “Small Business Cybersecurity Survey,” 2024.