Almost nobody reads privacy policies, which is exactly what some vendors count on when they collect and share more data than you would expect.
You signed up for a new HR platform last week. Maybe you needed better benefits administration or a slicker onboarding experience. You clicked through the setup screens, entered your company information, and somewhere between “Accept Terms” and “Get Started,” you sailed past a 47-page privacy policy without reading a single word.
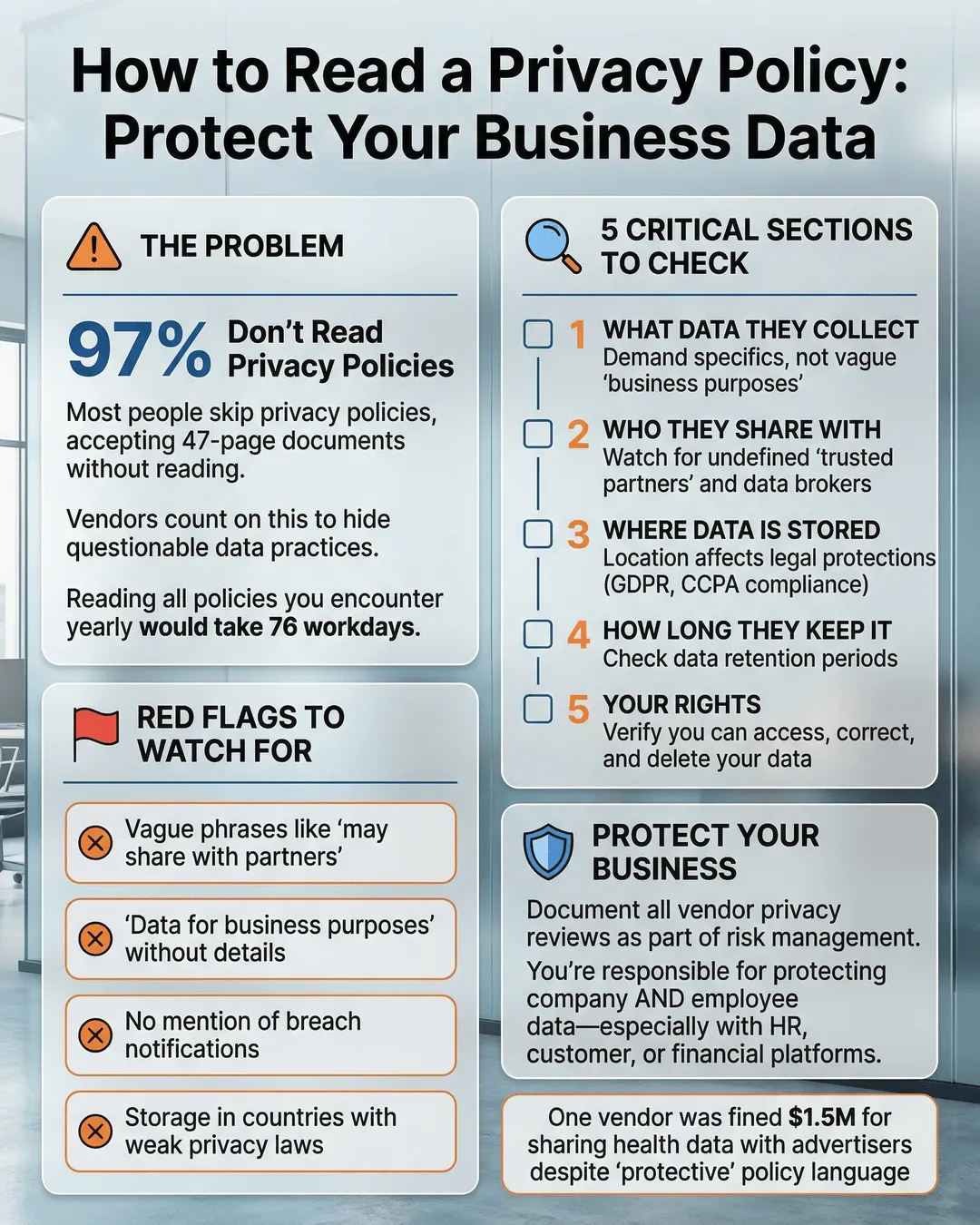
You’re not alone. Research shows that 97% of internet users accept privacy policies without reading them¹. The average privacy policy takes 18 minutes to read, and if you actually read every policy for every service you use, you’d spend 76 full workdays per year just reading legal documents². That’s not realistic, and vendors know it.
Some companies count on your hurried clicks. They bury concerning data practices in dense legal language, hoping you won’t notice that your employee information might be shared with third-party advertisers or that your business data could be stored on servers in countries with weak privacy protections.
But you don’t need a law degree to spot the warning signs. You just need to know where to look.
Key Takeaways
- Most vendors collect more data than necessary to provide their service, and many share that data with third parties for purposes beyond what you might expect.
- You can identify risky privacy policies by watching for vague language about data sharing, indefinite data retention periods, and broad claims to use your data for “business purposes.”
- Focus on five critical sections: what data is collected, how it’s used, who it’s shared with, how long it’s kept, and what happens if the company is sold.
- If a privacy policy uses phrases like “we may share data with partners” without naming those partners or specifying purposes, treat it as a red flag.
- Tools like browser extensions and AI summarizers can help you quickly identify concerning clauses without reading entire policies.
Why Privacy Policies Are Written to Confuse You
Privacy policies aren’t designed for readability. They’re legal documents written primarily to protect the company from liability, not to inform you about what actually happens to your data.
The average privacy policy is written at a college reading level, but it gets worse. Legal teams pack these documents with conditional language (“we may,” “we might,” “in some cases”), which gives the company maximum flexibility to change practices without updating the policy. They use terms like “business partners” and “service providers” without defining who these entities are or what they do with your information.
This isn’t always malicious. Sometimes it’s just lawyers being lawyers. But the effect is the same. You can’t make an informed decision about your company’s data when the policy describing how that data will be handled is deliberately opaque.
One study found that 81% of privacy policies contain at least one clause that contradicts what the company claims in its marketing materials³. The disconnect between “we respect your privacy” on the homepage and “we share your data with hundreds of partners” in paragraph 47 of the policy is real and common.
The Five Critical Sections You Must Read
You don’t need to read every word of a privacy policy. Focus on these five sections, which reveal the most about how a vendor will actually treat your data.
What Data They Collect
Look beyond the obvious. Yes, they’ll collect your name and email address. But what else?
Watch for phrases like “device identifiers,” “behavioral data,” “usage patterns,” or “metadata.” These terms often mean the vendor is collecting information about how your employees use the software, what features they click on, how long they spend on each page, and sometimes even keystrokes or mouse movements.
Some vendors collect data from third-party sources. If the policy mentions “data enrichment” or “information from data brokers,” the company is buying additional information about you or your employees from external sources to supplement what you provide directly.
Red flag language includes “we may collect” (which means they might collect anything) or long lists of data types that seem unrelated to the service. If you’re signing up for expense reporting software, why does it need access to your employees’ social media profiles?
How They Use Your Data
The use section tells you what the vendor actually does with the information they collect. Legitimate uses include providing the service, improving the product, and sending you necessary communications.
Concerning uses include “personalized advertising,” “marketing purposes,” “business development,” or the vague catch-all “to improve our business operations.” These phrases often mean your data will be analyzed, packaged, and potentially monetized in ways that don’t benefit you.
Watch for language about “training machine learning models” or “developing AI products.” Some vendors use customer data to build proprietary algorithms or products they then sell to other companies. You might be providing free training data for their next commercial offering.
If the policy says they use data “for any lawful purpose,” that’s essentially a blank check. Lawful doesn’t mean ethical or expected. It just means not illegal.
Who They Share It With
This is often the most alarming section. Modern software rarely operates in isolation. Most vendors share data with some third parties. The question is who, why, and under what terms.
Acceptable sharing includes cloud hosting providers (like AWS or Azure) who need access to store your data, payment processors who handle transactions, and specific named service providers who perform defined functions like email delivery or customer support.
Red flags include “advertising partners,” “analytics providers” (without naming specific companies), “affiliates” (which could mean dozens of related companies you’ve never heard of), or “other third parties” without further specification.
The most concerning language is “we may share your information with partners for their own business purposes.” This means your data could be used by other companies to build their own products, market their own services, or even sold again to additional parties.
Some policies claim the right to share “de-identified” or “aggregated” data freely. While this sounds safe, research shows that de-identified data can often be re-identified, especially when combined with other publicly available information⁴. Aggregated data might seem harmless until you realize your company is the only one in your industry and region using this software, making your aggregated data essentially identifiable.
How Long They Keep It
Many vendors keep your data far longer than necessary. Some keep it indefinitely.
Look for specific retention periods tied to business purposes. Good policies say things like “we retain transaction data for seven years to comply with tax regulations” or “we delete account information 90 days after you close your account.”
Bad policies use phrases like “as long as necessary for our business purposes,” “for as long as required by law” (without specifying which laws or time periods), or “indefinitely.”
Remember that data you can’t delete is data that remains at risk. The longer a vendor keeps your information, the more opportunities exist for breaches, unauthorized access, or policy changes that put your data to new uses you never approved.
What Happens During Acquisitions
This section is often buried deep in the policy, but it matters. When companies are acquired, customer data is frequently part of the deal.
Most policies reserve the right to transfer your data to a new owner if the company is sold. This means the privacy promises you relied on when you signed up could evaporate overnight if a new company with different values takes over.
Better policies commit to notifying customers of ownership changes and giving them the option to delete their data before the transfer. Poor policies simply state “we may transfer your information to a successor entity” with no additional protections.
Red Flags That Should Make You Think Twice
Beyond the five critical sections, watch for these warning signs that suggest a vendor’s privacy practices might not align with your expectations.
Vague language about data sharing is the biggest red flag. Phrases like “we work with partners” or “we share data with service providers” without naming those partners or providers should concern you. Legitimate vendors can and should specify who they share data with and why.
Broad consent clauses that ask you to agree to future policy changes without notification essentially give the company permission to rewrite the rules whenever they want. Look for language like “we may update this policy at any time” without promises to notify you of material changes.
Minimal user rights indicate a vendor that sees your data as their asset, not yours. Good policies clearly explain how you can access, correct, export, and delete your data. Poor policies make these rights difficult to exercise or don’t mention them at all.
Hidden jurisdiction clauses can subject your data to laws you didn’t expect. If your vendor is based in a country with weak privacy protections or operates data centers in multiple jurisdictions, your information might not receive the legal protections you assume.
Excessive data collection that goes far beyond what the service requires is a sign the vendor has business models beyond just selling you software. If a simple scheduling tool asks for access to your entire contact list, call logs, and location history, question why.
Practical Tools and Strategies
Reading privacy policies doesn’t have to consume your entire day. Here are practical approaches that work.
Use privacy policy summarizers. Browser extensions like Privacy Badger and ToS;DR (Terms of Service; Didn’t Read) automatically analyze and rate privacy policies, highlighting concerning clauses⁵. These tools won’t catch everything, but they’ll flag major issues quickly.
Search for keywords. Open the policy PDF or webpage and search for terms like “share,” “partners,” “third party,” “advertising,” “sell,” and “retention.” Reading just the sentences containing these keywords will reveal 80% of what you need to know.
Compare to alternatives. If you’re evaluating multiple vendors, put their privacy policies side by side. The vendor who is transparent about specific data uses, names their partners, and commits to limited retention is probably safer than the one hiding behind vague language.
Ask direct questions. Email the vendor’s privacy team with specific questions. “Which third-party analytics providers do you share data with?” or “How long do you retain employee records after an account is deleted?” If they won’t answer clearly, you have your answer about their transparency.
Negotiate terms. Enterprise contracts often allow you to negotiate data protection terms beyond what the standard privacy policy offers. You can sometimes require vendors to limit data sharing, specify retention periods, or commit to data residency in specific regions.
Check their track record. Search for “[company name] data breach” and “[company name] privacy complaint.” Past behavior often predicts future practices. A vendor with multiple breaches or regulatory actions is a higher risk than one with a clean record.
What to Do When You Find Concerning Practices
You’ve read the policy. You found red flags. Now what?
First, assess the risk in context. Not every concerning practice is a deal-breaker. Consider what data you’re actually sharing, how sensitive it is, and what harm could come from misuse. Sharing employee names to a scheduling tool is different from sharing employee health records to a benefits platform.
Second, look for alternatives. The market offers multiple solutions for most business needs. If one vendor’s privacy practices concern you, competitors might offer similar functionality with better data protection.
Third, implement compensating controls. If you must use a vendor with less-than-ideal privacy practices, minimize the data you share. Don’t give them access to everything just because they ask. Use separate email addresses for vendor communications. Avoid integrating more systems than necessary.
Fourth, document your decision. If you choose to proceed despite privacy concerns, document why. What business need justified accepting this risk? What alternatives did you consider? This documentation protects you if questions arise later about why you selected this vendor.
Finally, monitor and reassess. Privacy policies change. Companies get acquired. Add vendor privacy reviews to your annual risk assessment process. What was acceptable last year might not be acceptable now.
Building a Vendor Privacy Assessment Process
Smart organizations don’t evaluate privacy policies only during initial vendor selection. They build ongoing assessment into their procurement and vendor management processes.
Create a standard questionnaire that every vendor must complete before contract signature. Include specific questions about data collection, sharing, retention, and security practices. Require vendors to name their sub-processors and data center locations.
Establish minimum privacy requirements. Decide what practices are non-negotiable for your organization. Maybe you require all vendors to allow data export, commit to maximum retention periods, or prohibit selling customer data to third parties.
Tier vendors by data sensitivity. Not every vendor needs the same scrutiny. Tools that only access non-sensitive data might receive lighter review than systems handling employee financial or health information.
Schedule regular re-assessments. Privacy practices change faster than most contract terms. Review your highest-risk vendors annually and all vendors at least every three years.
Train your team. Make sure everyone involved in vendor selection knows what to look for in privacy policies. Finance teams selecting expense software and HR teams choosing benefits platforms need the same privacy awareness as your IT department.
Conclusion
You will never read every word of every privacy policy for every service your company uses. That’s unrealistic, and vendors know it.
But you can protect your organization by getting strategic about where you focus your attention. Prioritize vendors who will handle your most sensitive data. Learn to spot the red flags that signal concerning practices. Ask direct questions and don’t accept vague answers.
The vendors who respect your privacy will make it easy to understand their practices. They’ll use clear language, name their partners, specify retention periods, and give you meaningful control over your data. The ones who bury concerning practices in legal jargon are showing you who they are.
Your data and your employees’ data deserve protection. That starts with actually understanding what you’re agreeing to when you click “Accept.”
Citations
- Deloitte, “Consumer Privacy and Trust Survey,” 2024.
- Carnegie Mellon University, “The Cost of Reading Privacy Policies,” 2024.
- Federal Trade Commission, “Privacy Policy Analysis Report,” 2023.
- Nature Communications, “Re-identification Risks in Modern Data Sets,” 2024.
- Electronic Frontier Foundation, “Privacy Tools and Best Practices,” 2024.