Most People Don't Know This About SOC2 Compliance
You have heard the term “SOC2” thrown around in vendor conversations, contract negotiations, and security meetings. But what does it actually mean for your business?
SOC2 compliance is not just another checkbox on your IT to-do list. It is a framework that proves your organization handles customer data responsibly. For SMBs working with enterprise clients or storing sensitive information, SOC2 has become the baseline expectation, not a nice-to-have credential.
Understanding SOC2 can unlock new business opportunities, strengthen customer trust, and protect your organization from data breaches. This guide breaks down everything you need to know about SOC2 compliance, from basic definitions to implementation strategies.
Key Takeaways
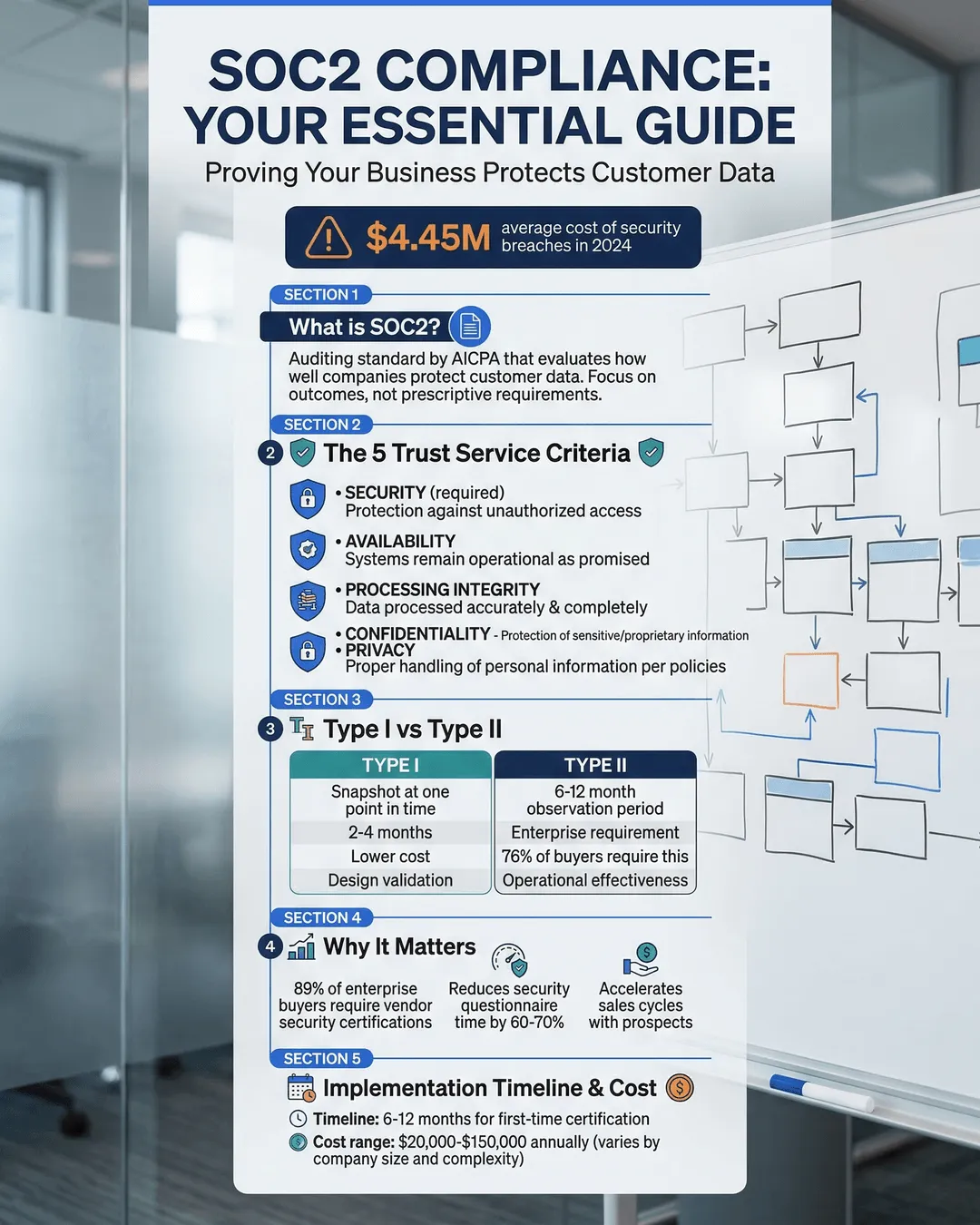
- SOC2 is a voluntary compliance framework developed by the American Institute of CPAs (AICPA) that validates how organizations manage customer data based on five trust service criteria.
- Type I reports evaluate security controls at a single point in time, while Type II reports assess controls over a period of at least six months.
- The five trust service criteria are security (mandatory), availability, processing integrity, confidentiality, and privacy.
- SOC2 compliance typically takes 3-6 months for initial certification and requires ongoing maintenance through continuous monitoring and annual audits.
- Achieving SOC2 can increase revenue opportunities by 30-40% for B2B SaaS companies seeking enterprise clients.¹
What SOC2 Compliance Actually Means
SOC2 stands for Service Organization Control 2. It is an auditing standard created by the AICPA that focuses specifically on how service providers manage and protect customer data.
Unlike regulatory requirements such as HIPAA or GDPR, SOC2 is voluntary. Organizations pursue it to demonstrate their commitment to data security and operational excellence. The framework evaluates your internal controls against specific trust service criteria.
The audit results in a report prepared by an independent CPA firm. This report details how well your organization meets the selected trust service criteria. Potential clients and partners review these reports during vendor assessments to evaluate risk.
SOC2 applies primarily to technology and cloud-based service providers. If your business stores, processes, or transmits customer data, you are a candidate for SOC2 compliance.
Who Needs SOC2 Compliance
Your organization should consider SOC2 if you fall into these categories:
SaaS providers offering cloud-based software solutions to other businesses need SOC2 to win enterprise contracts. Many Fortune 500 companies will not sign agreements with vendors lacking SOC2 certification.
Data centers and hosting providers managing infrastructure for clients require SOC2 to prove they safeguard physical and digital assets properly.
Managed service providers handling IT operations, security monitoring, or business processes for clients need SOC2 to demonstrate operational reliability.
Financial technology companies processing payments or storing financial data face intense scrutiny. SOC2 provides third-party validation of security practices.
Healthcare technology vendors storing protected health information should pursue both SOC2 and HIPAA compliance. The frameworks complement each other.
If your potential clients ask for security questionnaires or request audit reports during procurement, you need SOC2. The absence of certification often eliminates you from consideration before conversations begin.
The Five Trust Service Criteria Explained
SOC2 evaluates your controls based on five trust service criteria. Security is mandatory for all SOC2 audits. The other four criteria are optional based on your business model and customer requirements.
Security (Mandatory)
Security forms the foundation of every SOC2 audit. This criterion examines how you protect systems and data from unauthorized access, both physical and logical.
Your auditor evaluates access controls, network security, system monitoring, incident response procedures, and vulnerability management. You must demonstrate that only authorized individuals can access sensitive data and that you detect and respond to security incidents promptly.
Common controls include multi-factor authentication, encryption of data at rest and in transit, regular penetration testing, and documented security policies.
Availability
Availability measures whether your systems and services remain accessible and operational as promised. This criterion matters for businesses offering uptime guarantees in service level agreements.
Your auditor reviews disaster recovery plans, backup procedures, system redundancy, performance monitoring, and incident management processes. You need evidence that you can maintain operations during disruptions and recover quickly from outages.
Organizations typically implement redundant infrastructure, automated failover mechanisms, and regular backup testing to meet availability requirements.
Processing Integrity
Processing integrity confirms that your systems process data completely, accurately, and on time as intended. This criterion is critical for organizations handling transactions, calculations, or data transformations.
The audit examines quality assurance processes, error detection and correction mechanisms, data validation controls, and system change management. You must prove that your systems deliver correct outputs without unauthorized modifications.
Financial services companies, payment processors, and analytics platforms commonly include this criterion in their SOC2 scope.
Confidentiality
Confidentiality addresses how you protect information designated as confidential. This goes beyond general security controls to focus on data classification, handling procedures, and disposal methods.
Your auditor reviews data classification schemes, confidentiality agreements, access restrictions based on data sensitivity, and secure deletion practices. You need policies defining what constitutes confidential data and procedures ensuring only authorized parties access it.
This criterion applies when you handle proprietary business information, trade secrets, or other sensitive non-public data beyond standard customer information.
Privacy
Privacy focuses on the collection, use, retention, disclosure, and disposal of personal information. This criterion aligns with privacy regulations and examines your entire data lifecycle.
The audit evaluates privacy notices, consent mechanisms, data subject rights processes, third-party data sharing agreements, and retention policies. You must demonstrate compliance with your stated privacy practices and applicable privacy laws.
Organizations handling significant volumes of personally identifiable information typically include privacy in their SOC2 scope. This criterion has become more important as privacy regulations expand globally.
SOC2 Type I vs Type II: Understanding the Difference
SOC2 audits come in two varieties. The difference between Type I and Type II reports significantly impacts the value and credibility of your certification.
Type I Reports
A Type I report evaluates your controls at a single point in time. The auditor examines whether you have designed appropriate controls to meet the selected trust service criteria.
Think of Type I as a snapshot. It proves that on a specific date, you had the right policies, procedures, and controls in place. The auditor does not test whether these controls operated effectively over time.
Type I reports typically take 1-2 months to complete. They cost less than Type II audits and serve as a stepping stone for organizations new to SOC2 compliance.
However, Type I reports carry limited weight with sophisticated buyers. They prove you designed controls but not that you use them consistently. Most enterprise clients require Type II reports for vendor approval.
Type II Reports
A Type II report evaluates both the design and operating effectiveness of your controls over a period of time. The standard audit period is six months, though some organizations extend this to twelve months.
The auditor tests whether your controls functioned as designed throughout the entire period. They review logs, interview staff, observe processes, and collect evidence of consistent control operation.
Type II reports take 3-6 months to complete from readiness through final report issuance. They require more extensive documentation and testing, which increases costs.
But Type II reports carry significantly more credibility. They demonstrate sustained commitment to security and operational excellence. According to recent surveys, 87% of enterprise buyers require Type II reports when evaluating new vendors.²
Your first SOC2 audit will almost always be Type I. Organizations typically achieve Type I certification, operate under those controls for six months, and then pursue Type II certification.
The SOC2 Compliance Process: Step by Step
Achieving SOC2 certification requires planning, preparation, and persistence. The process involves multiple phases spanning several months.
Phase 1: Scoping and Gap Analysis
Start by defining your audit scope. Determine which trust service criteria apply to your business. Identify the systems, processes, and locations the audit will cover.
Conduct a gap analysis comparing your current controls against SOC2 requirements. Most organizations discover gaps in documentation, monitoring, or formal policies.
You can perform this analysis internally or hire a consultant. External consultants with SOC2 expertise accelerate the process and provide objective assessments.
Budget 4-8 weeks for scoping and gap analysis. The findings drive your remediation roadmap.
Phase 2: Remediation and Control Implementation
Address the gaps identified in phase one. This typically involves implementing new controls, documenting existing informal processes, and enhancing monitoring capabilities.
Common remediation activities include:
Developing formal security policies covering access control, incident response, change management, and risk assessment. Creating employee training programs on security awareness and compliance requirements. Implementing technical controls such as encryption, logging, and vulnerability scanning. Establishing vendor management processes to evaluate third-party service providers.
Remediation timelines vary based on gap severity. Organizations with mature security programs may need 1-2 months. Companies starting from scratch might require 4-6 months.
Do not rush this phase. Implementing controls properly the first time prevents audit failures and reduces long-term compliance costs.
Phase 3: Auditor Selection
Choose a CPA firm qualified to perform SOC2 audits. Not all accounting firms offer this service. Look for firms with relevant industry experience and references from similar organizations.
Request proposals from multiple auditors. Compare pricing, timelines, and communication approaches. The cheapest option often creates headaches through poor communication and extended timelines.
Your auditor becomes a partner in the certification process. Select a firm that explains requirements clearly and provides practical guidance.
Budget 2-4 weeks for auditor selection and contract negotiation.
Phase 4: Readiness Assessment
Before the formal audit begins, conduct an internal readiness assessment. Test your controls, review documentation completeness, and verify evidence collection processes.
Many organizations perform a pre-audit with their chosen auditor. This unofficial assessment identifies remaining gaps before the official audit starts. Pre-audits reduce the risk of audit failures and scope extensions.
Your auditor cannot provide remediation advice during the official audit. The readiness phase is your opportunity to ask questions and refine controls.
Plan 2-4 weeks for readiness assessment activities.
Phase 5: Formal Audit
The formal audit begins when your auditor starts collecting and testing evidence. For Type I audits, this involves reviewing documentation and interviewing personnel about control design.
For Type II audits, auditors examine evidence spanning the entire audit period. They review access logs, change management tickets, vulnerability scan results, and incident response records. They test that controls operated consistently throughout the period.
Respond promptly to auditor requests. Delays in providing evidence extend the timeline and increase costs. Assign a dedicated point of contact to manage auditor communications.
The formal audit phase typically takes 3-6 weeks for Type I and 6-10 weeks for Type II.
Phase 6: Report Issuance
After completing fieldwork, your auditor drafts the SOC2 report. This document describes your system, outlines the controls tested, and presents the auditor’s opinion on control effectiveness.
You review the draft report for accuracy. The auditor addresses any questions or concerns about the findings. Once finalized, you receive the official SOC2 report.
This report is confidential. You share it with customers and prospects under non-disclosure agreements. The report provides detailed information about your security posture that you would not publish publicly.
Report issuance typically occurs 2-4 weeks after audit fieldwork concludes.
Costs and Timeline for SOC2 Certification
SOC2 compliance represents a significant investment in time and money. Understanding the costs helps you budget appropriately and set realistic expectations.
Financial Costs
Audit fees vary based on organization size, system complexity, and the number of trust service criteria in scope. Small companies pursuing Type I certification might pay $15,000-$30,000. Mid-sized organizations seeking Type II reports typically spend $30,000-$75,000. Large enterprises with complex environments can exceed $100,000 annually.³
Beyond audit fees, budget for internal costs:
Consultant fees for gap analysis and remediation guidance range from $20,000-$60,000. Technology investments in logging, monitoring, and security tools might require $10,000-$50,000. Employee time for documentation, evidence collection, and audit support represents hidden costs. Organizations often underestimate the internal effort required.
Annual maintenance costs include ongoing auditor fees, continuous monitoring tools, and dedicated compliance personnel. Plan for 50-75% of your initial certification costs annually to maintain compliance.
Time Investment
From initial planning to report issuance, expect 3-6 months for Type I certification. Type II certification requires 9-12 months when you include the six-month operating period before the audit begins.
Organizations with mature security programs and dedicated resources can sometimes accelerate these timelines. Companies starting from scratch or lacking internal expertise often need longer.
Your first audit takes the longest. Subsequent annual audits proceed faster because your controls and documentation are established. Renewal audits typically complete in 2-4 months.
Factors Affecting Cost and Timeline
Several variables influence your SOC2 journey:
The number of trust service criteria in scope directly impacts complexity. Security-only audits cost less than audits covering all five criteria.
System complexity matters. Organizations with multiple data centers, numerous integrations, or complex infrastructure face longer audits and higher costs.
Internal readiness significantly affects timelines. Companies with documented policies and established controls move faster than those building programs from scratch.
Auditor responsiveness and your team’s availability for evidence collection either accelerate or delay the process.
Maintaining SOC2 Compliance After Certification
Achieving your first SOC2 report is an accomplishment. But compliance is not a one-time project. It requires ongoing effort to maintain certification and prepare for annual audits.
Continuous Monitoring
Implement continuous monitoring of your security controls. Automated tools track access logs, system changes, vulnerability scans, and security incidents. Regular monitoring identifies control failures before they become audit findings.
Assign responsibility for monitoring activities. Many organizations appoint a compliance manager or security team to oversee ongoing requirements. This person tracks control evidence, manages policy updates, and coordinates with auditors.
Quarterly internal audits help verify controls operate as designed. Test key controls, review documentation completeness, and address any gaps before the annual audit begins.
Policy and Procedure Updates
Your environment changes throughout the year. New systems launch, employees join and leave, vendors are added, and business processes evolve. Update your policies and procedures to reflect these changes.
Schedule annual policy reviews even if significant changes have not occurred. This ensures your documentation remains accurate and relevant.
Document all changes to systems and processes. Your auditor will review change management records during the next audit. Missing or incomplete change documentation creates audit issues.
Employee Training
Security awareness training is not optional. All employees need regular updates on security policies, acceptable use guidelines, and incident reporting procedures.
New employees should receive security training during onboarding. Annual refresher training keeps security top of mind for existing staff.
Document all training activities. Your auditor will verify that employees receive appropriate security education. Training records serve as evidence of your commitment to security culture.
Vendor Management
If you rely on third-party vendors for critical services, monitor their compliance status. Request updated SOC2 reports from vendors handling customer data. Evaluate whether vendor security postures meet your requirements.
Maintain a vendor inventory documenting all third parties with access to your systems or data. Review this inventory quarterly and terminate unused vendor relationships.
Vendor security failures can become your security failures. Due diligence on vendors protects your organization and maintains compliance.
Preparing for Annual Audits
Start preparing for your next audit immediately after completing the current one. Maintain organized evidence files throughout the year. Collect and store logs, tickets, reports, and documentation in a centralized location.
Three months before your audit begins, conduct an internal readiness assessment. Test controls, verify evidence completeness, and address any gaps discovered.
Schedule your audit engagement early. Auditors have busy seasons and limited availability. Booking your audit slot 3-4 months in advance ensures you get your preferred timeline.
Common SOC2 Challenges and How to Overcome Them
Organizations pursuing SOC2 certification encounter predictable obstacles. Anticipating these challenges helps you navigate them successfully.
Documentation Overload
SOC2 requires extensive documentation. Policies, procedures, system descriptions, risk assessments, and evidence files pile up quickly. Many organizations struggle with documentation organization and maintenance.
Start with templates. Industry-standard policy templates provide a foundation you can customize. Do not write every document from scratch.
Use a compliance management platform. These tools centralize documentation, track policy versions, manage evidence collection, and generate reports. Popular platforms include Vanta, Drata, and Tugboat Logic.
Focus on quality over quantity. Auditors value clear, concise documentation more than lengthy documents full of boilerplate text. Write policies your employees will actually read and follow.
Resource Constraints
Small and mid-sized businesses often lack dedicated security or compliance teams. Existing staff juggle SOC2 requirements alongside their regular responsibilities.
Consider hiring a fractional compliance officer or security consultant. These professionals provide expertise without full-time employment costs. They guide your team through the process and fill knowledge gaps.
Prioritize ruthlessly. Not every control requires equal attention. Focus on high-impact controls that directly address your biggest risks.
Automate where possible. Security tools that automatically collect evidence reduce manual work. Invest in automation early to minimize ongoing effort.
Control Gaps in Inherited Systems
You may inherit systems or processes from before you understood SOC2 requirements. Legacy systems often lack logging, access controls, or documentation necessary for compliance.
Create a remediation roadmap. You cannot fix everything immediately. Prioritize systems based on risk and customer data sensitivity.
For systems you cannot remediate quickly, implement compensating controls. If a system lacks granular access logs, increase monitoring through other means such as network traffic analysis or endpoint detection tools.
Document your remediation plan. Auditors appreciate transparency about known gaps and your timeline for addressing them. A clear plan demonstrates commitment to continuous improvement.
Audit Fatigue
The first SOC2 audit is intense. Evidence requests seem endless. Auditors ask detailed questions about controls. Your team may experience burnout from the effort required.
Set realistic expectations with your team. Explain that the first audit requires significant effort, but subsequent audits become more manageable.
Establish sustainable processes from the beginning. Build evidence collection into regular workflows rather than scrambling during audit season.
Celebrate milestones. Recognize your team’s effort at each phase completion. SOC2 certification is a genuine achievement worth acknowledging.
Conclusion
SOC2 compliance has evolved from a differentiator to a requirement for SMBs serving enterprise clients or handling sensitive data. The framework provides independent validation that you take data security seriously and operate with integrity.
The journey to certification demands investment in time, money, and organizational commitment. But the benefits extend beyond checking a box on customer security questionnaires. SOC2 forces you to formalize security practices, document processes, and build a culture of compliance.
Your first audit will challenge you. You will discover gaps in documentation, controls, and processes. You will invest hours collecting evidence and answering auditor questions. But you will emerge with a stronger security posture and a competitive advantage in your market.
Start your SOC2 journey by defining your scope and conducting a gap analysis. Address the most critical gaps first. Choose an experienced auditor who can guide you through the process. And remember that compliance is ongoing, not a destination.
The organizations that treat SOC2 as a continuous improvement program rather than a one-time project build sustainable competitive advantages. They win larger deals, retain customers longer, and suffer fewer security incidents. SOC2 compliance is an investment in your company’s future growth and resilience.
Citations
- Paddle, “The Business Impact of SOC2 Compliance for B2B SaaS Companies,” 2024.
- Gartner, “Vendor Risk Management Survey,” 2024.
- CPA Practice Advisor, “SOC2 Audit Pricing Guide,” 2024.